Save to My DOJO
Table of contents
In How to reset the root password for VCSA 6.x, I illustrated how the root password on vCSA 6.x can be reset if you ever got locked out. Likewise, you may end up with a locked SSO domain account. In How to better secure your vCenter SSO domain passwords, I described how the Password and Lockout policies govern the creation and behavior of SSO domain accounts. Depending on the applied lockout policy settings, any SSO account assigned to you could end up locked following a number of failed login attempts whether intentional or not. Unless automatic unlocking is enforced via policy, the only way to unlock an SSO user account is to have an administrator do it for you using the vSphere Web client. In today’s post, we see how you can achieve the same result using command line tools instead.
Using vdcadmintool
You might be faced with a situation where you are unable to connect to vCenter using the vSphere Web client maybe because the corresponding processes are down. Additionally, you might have applications or scripts configured to connect to vCenter via SSO domain accounts. If for whatever reason these accounts end up locked, applications or scripts with such a dependency will invariably stop working. Thus, being able to unlock accounts using alternative methods is imperative. An example of an SSO domain account is [email protected].
The vdcaadmintool is one command line tool you can use to unlock an SSO account. The following procedure works on both vCenter Server 6.x for Windows and the appliance version (vCSA).
On vCSA 6.x
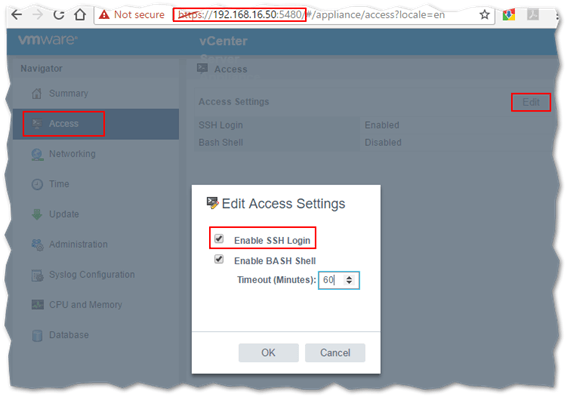
Step 1 – Make sure SSH access to vCSA is enabled via VAMI (https://<vCSA IP address>:5480). Log in as root and navigate to the Access page. Click on the Edit button and Enable SSH Login if applicable.
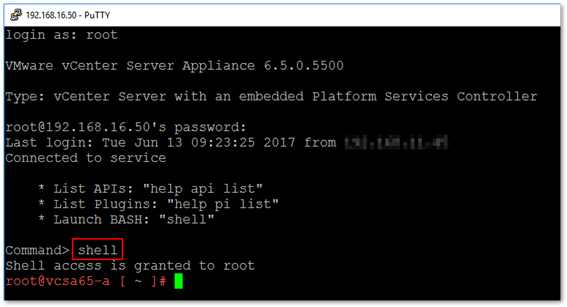
Step 2 – Using putty or similar, SSH to the vCSA and log in as root. After you log in, type shell to launch BASH.
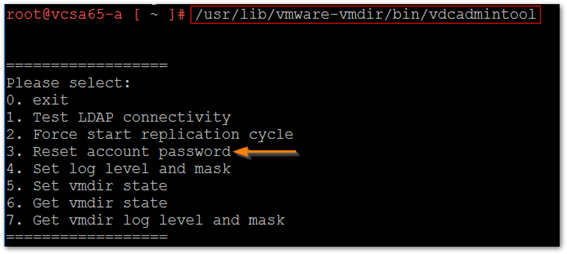
Step 3 – Run the following command: /usr/lib/vmware-vmdir/bin/vdcadmintool and select option 3.
Step 4 – Type the full username at the Please enter account UPN prompt. The default SSO domain is set to vsphere.local. If you changed this during installation, add the custom domain to the targeted account instead. For this example, I’ll be unlocking [email protected].
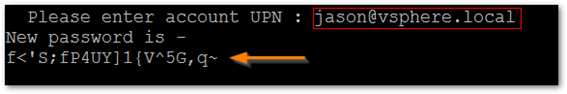
Note: The tool, besides unlocking the account, will also reset its password as shown above.
On vCenter Server for Windows
The same exact procedure is applicable to vCenter Server 6.x for Windows. The only differences are the path to the tool’s executable, this being “%VMWARE_CIS_HOME%\vmdird\vdcadmintool.exe and executing the tool within an administrative command prompt. Other than that, the same steps apply.
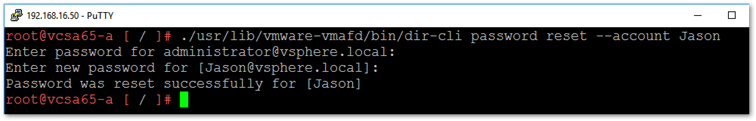
Using dir-cli
The dir-cli tool is available for both flavors of vCenter Server. On the Windows version, you’ll find the tool under C:\Program Files\VMware\vCenter Server\vmafdd\dir-cli.exe while on vCSA the path is /usr/lib/vmware-vmafd/bin/dir-cli. The tool has many applications including SSO account creation, password changes and resetting, certificate management and so on. The command reference can be viewed here.
Like the previous tool described, dir-cli automatically unlocks a locked account when its password is reset. Again, we need to run the tool while logged in as root (or equivalent) via SSH or from a command prompt in case of vCenter for Windows. To reset a password for a specific account, run dir-cli as shown. When specifying the account, do not add the domain bit – vpshere.local in this case. The tool fails to find the user account if you do since it automatically appends the domain to the user account specified.
I’ve targeted my test account which I locked in advance using PowerCLI. In the next video, I go through the process of demonstrating how to quickly lock an account with PowerCLI and how to spot a locked account using the vSphere Web client. I also illustrate the use of the two command line tools just described and how you can change the password for an SSO account using the vSphere Web Client.
That’s all I have for today. I hope you found the material presented interesting and useful. If you have any comments or suggestions, please feel free to drop me a line in the comments box below.


Not a DOJO Member yet?
Join thousands of other IT pros and receive a weekly roundup email with the latest content & updates!








