Save to My DOJO
Table of contents
- Plan for the Worst-Case Scenario
- Use all Available Software Security and Encryption Options
- Understand the Overlap Between Active Data Systems and Backup Retention Policies
- High Availability is a Goal, Not a Technology
- Backup and Disaster Recovery Strategies are Not the Same Thing
- Backup Applies to Everyone in an Organization, so Include Everyone
- One Backup is Never Enough
- One Size Does Not Fit All
- Test It. Then Test again. And Again…
- Backup and Disaster Recovery Planning is a Process, Not a One-Time Event
- Free eBook – The Backup Bible Complete Edition
In honour of the initial publication of The Backup Bible, I’ve extracted the top 10 most important messages from the book and compiled them into a handy reference.
The Backup Bible is a free eBook I wrote for Altaro that covers everything you need to know about planning, deploying and maintaining a secure and reliable backup and disaster recovery strategy. Download the Backup Bible Complete Edition now!
Plan for the Worst-Case Scenario
We have lots of innovative ways to protect our data. Using HCI or high-end SANs, we can create insanely fault-tolerant storage systems. We can drag files into a special folder on our computer and it will automatically create a copy in the cloud. Many document-based applications have integrated auto-saves and disk-backed temporary file mechanisms. All of these are wonderful technologies, but they can generate a false sense of security.
One specific theme drives all of my writing on backup: you must have complete, safe, separate duplicates. Nothing else counts. Many people think, “What if my hard drive fails?” and plan for that. That’s really one of your least concerns. Better questions:
- What if I make a mistake in my document and don’t figure it out for a few days?
- What if the nice lady in the next cubicle tries to delete her network files, but accidentally deletes mine?
- What if someone steals my stuff?
- What if my system has been sick but not dead for a while, and all my “saved” data got corrupted?
- What if I’m infected by ransomware?
Even the snazziest first-line defences cannot safeguard you from any of these things. Backups keep a historical record, so you can sift through your previous versions until you find one that didn’t have that mistake. They will also contain those things that should have never been removed. Backups can (and should) be taken offline where malicious villains can’t get to them.
Plan for the Worst Case-Scenario #Backup10Commandments #BackupBible – Tweet this
Use all Available Software Security and Encryption Options
Once upon a time, no one really thought about securing backups. The crooks realized that and started pilfering backup tapes. Worse, ransomware came along and figured out how to hijack backup programs to destroy that historical record as well.
Backup vendors now include security measures in their products. Put them to good use.
Use all Available Software Security and Encryption Options #Backup10Commandments #BackupBible – Tweet this
Understand the Overlap Between Active Data Systems and Backup Retention Policies
The longer you keep a backup, the taller the media stack gets. That means that you have to pay more for the products and the storage. You have to spend more time testing old media. You have to hold on to archaic tape drives and disk bus interfaces or periodically migrate a bunch of stale data. You might have ready access to a solution that can reduce all of that.
Your organization will establish various retention policies. In a nutshell, these define how long to keep data. For this discussion, let’s say that you have a mandate to retain a record of all financial transactions for a minimum of ten years. So, that means that you need to keep backup data until it’s ten years old, right? Not necessarily.
In many cases, the systems used to process data have their own storage mechanisms. If your accounting software retains information in its database and has an automatic process that keeps data for ten years and then purges it, then the backup that you captured last night has ten-year-old data in it.
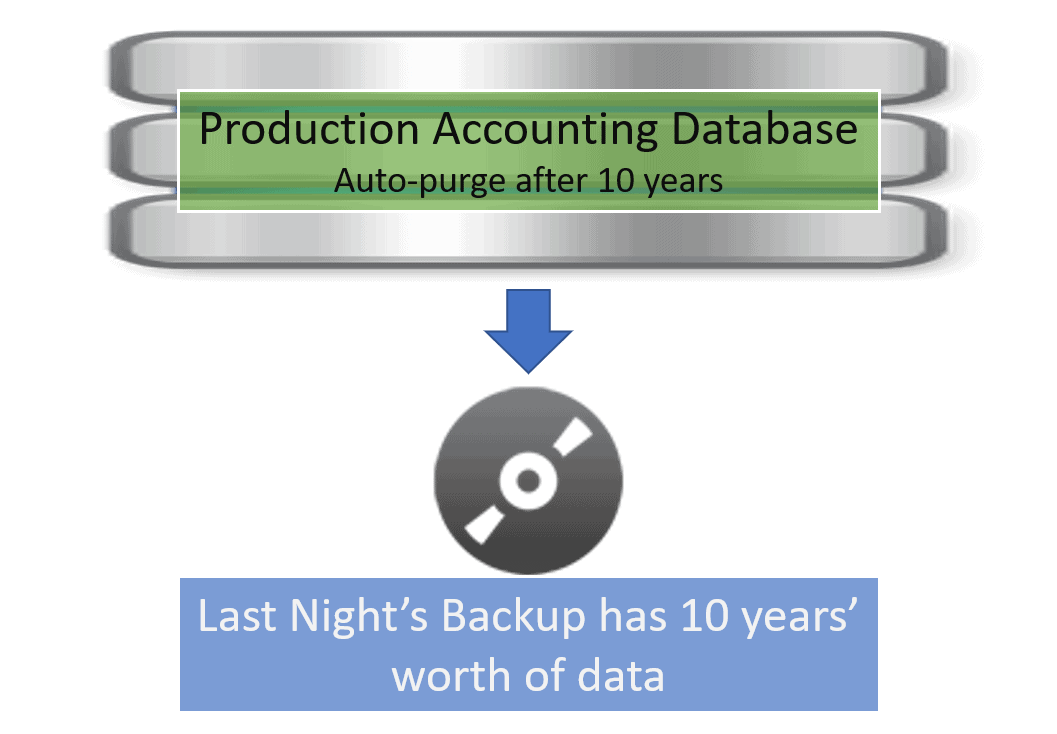
Does that satisfy your retention policy? Perhaps, perhaps not. Your retention policy might specifically state that backups must be kept for ten years, which does not take the data into consideration. Maybe you can go to management and get the policy changed, but you might also find out that it is set by law or regulation. Even if you are not bound by such restrictions, you might still have good reason to continue keeping backups long-term. Since we’re talking about a financial database, what if someone with tech skills and a bit too much access deletes records intentionally? Instead of needing to hide their malfeasance for ten years, they only need to wait out whatever punctuated schedule you come up with. Maybe accounting isn’t the best place to try out this space-saving approach.
Understand the Overlap Between Active Data Systems and Backup Retention Policies #Backup10Commandments #BackupBible – Tweet this
High Availability is a Goal, Not a Technology
We talk a lot about our high availability tech and how this is HA and that is HA. Really, we need to remember that “high availability” is a metric. How about that old Linux box running that ancient inventory system that works perfectly well but no one can even find? If it didn’t reboot last year, then it had 100% uptime. That fits the definition of “highly available”.
You can use a lot of fault-tolerant and rapid recovery technologies to boost availability, but a well-implemented backup and disaster recovery plan also helps. All of the time that people spend scrounging for tapes and tape drive manuals counts against you. Set up a plan and stick to it, and you can keep your numbers reasonable even in adverse situations.
High Availability is a Goal, Not a Technology #Backup10Commandments #BackupBible – Tweet this
Backup and Disaster Recovery Strategies are Not the Same Thing
If your disaster recovery plan is, “Take backups every night,” then you do not have a disaster recovery plan.
Backup is a copy of data and the relevant technologies to capture, store, and retrieve it. That’s just one piece of disaster recovery. If something bad happens, you will start with whatever is leftover and try to return to some kind of normal state. That means people, buildings, and equipment as much as it means important data.
The Backup Bible goes into much more detail about these topics.
Backup and Disaster Recovery Strategies are Not the Same Thing #Backup10Commandments #BackupBible – Tweet this
Backup Applies to Everyone in an Organization, so Include Everyone
The servers and backup systems live in the IT department (or the cloud), but every department and division in the organization has a stake in its contents and quality. Keep them invested and involved in the state of your backup and disaster recovery systems.
Backup Applies to Everyone in an Organization, so Include Everyone #Backup10Commandments #BackupBible – Tweet this
One Backup is Never Enough
I said in the first commandment that for a proper backup, you must have complete, safe, separate duplicates. A single duplicate is a bare minimum, but it’s not enough. Backup data gets corrupted or stolen just as readily as anything else. You need multiple copies to have any real protection.
Whether you take full backups every week or every month, take them frequently. Keep them for a long time.
One Backup is Never Enough #Backup10Commandments #BackupBible – Tweet this
One Size Does Not Fit All
It would be nice if we could just say, “Computer, back up all my stuff and keep it safe.” Maybe someday soon we’ll be able to do that for our personal devices. It’s probably going to be a bit longer before we can use that at the enterprise scale. In the interim, we must do the work of figuring out all the minutiae. Until we have access to a know-it-all-program and a bottomless storage bucket, we need to make decisions about:
- Using different retention policies on different types of data
- Using different storage media and locations
- Overlapping different backup applications to get the most out of their strengths
As an example of the last one, I almost always configure Microsoft SQL to capture its own backups to a network location and then pull the .bak files with a fuller program. Nobody really backs up and restores Microsoft SQL as well as Microsoft, but just about everyone has better overall backup features. I don’t have to choose.
One Size Does Not Fit All #Backup10Commandments #BackupBible – Tweet this
Test It. Then Test again. And Again…
Your backup data is, at best, no better than it was the last time that you tested it. If you’ve never tested it, then it might just be a gob of disrupted magnetic soup. Make a habit of pulling out those old backups and trying to read from them. Your backup program probably has a way to make this less tedious. Set bi-annual or quarterly reminders to do this.
Test It. Then Test again. And Again… #Backup10Commandments #BackupBible – Tweet this
Backup and Disaster Recovery Planning is a Process, Not a One-Time Event
The most important and most often overlooked aspect of all backup and disaster recovery planning is employing a “set and forget” mentality. Did you set up a perfect backup and disaster recovery plan five years ago? Awesome! How much of the things that were true then are true now? If it’s less than 100%, your plan needs some updating. Make a scheduled recurring event to review and update the backup process. Remember the 6th commandment. Hint: If you feed them, they will come.
Backup and Disaster Recovery Planning is a Process, Not a One-Time Event #Backup10Commandments #BackupBible – Tweet this
Free eBook – The Backup Bible Complete Edition
I’d love to be able to tell you creating a backup and disaster recovery strategy is simple but I can’t. It takes time to figure out your unique backup requirements, business continuity needs, software considerations, operational restrictions, etc. and that’s just the start. I’ve been through the process many, many times and as such Altaro asked me to put together a comprehensive guide to help others create their own plan.
The Backup Bible Complete Edition features 200+ pages of actionable content divided into 3 core parts, including 11 customizable templates enabling you to create your own personalized backup strategy. It was a massive undertaking but hopefully, it will help a lot of people protect their data properly and ensure I hear a fewer data-loss horror stories from the community!


Not a DOJO Member yet?
Join thousands of other IT pros and receive a weekly roundup email with the latest content & updates!