Save to My DOJO
Each release of the Windows Server operating system represents a milestone of new technologies, capabilities, and features that help organizations solve the present technology challenges facing businesses. Windows Server 2022 is a milestone release of Windows Server. It combines powerful features across the board to allow companies to implement both on-premises technologies and easily extend their infrastructure with a hybrid configuration, with resources housed in Azure.
Arguably, one of the most critical challenges facing most businesses today is security. Windows Server 2022 represents the most advanced Windows Server operating system in terms of security features and advancements. This overview will look at the Windows Server 2022 security features and enhancements that help advance your organization’s security to the next level.
Overview of Windows Server 2022 Security Features
There are many great new Windows Server 2022 security features to note. Windows Server 2022 introduces new concepts and features, building on previous improvements with Windows Server 2019 hybrid features and security innovations. Note the following overview of new security features:
-
- Secured-core server
- Simplified configuration tools
- Secure connectivity
- Hybrid management tools
- Windows Server 2022 Azure Edition hotpatching
Let’s examine each of these enhancements with Windows Server 2022 and see how they bring security features forward to help meet the current threat landscape and help businesses seamlessly control and secure both on-premises and cloud resources.
Secured-core server
Microsoft first started the secured-core offering to the world of PC. However, with the apparent benefits from the client-side, this technology has been brought to Windows Server. So what is the Secured-Core technology now included in Windows Server 2022?
Secured-Core security technology is built upon three different pillars that Microsoft uses to make up the Secured-Core platform. These include:
-
- Simplified security
-
- Advanced protection
-
- Preventative defense
What does Secured-Core mean from the Windows Server 2022 perspective?
Simplified Security
MICROSOFT requires certain OEM specifications and capabilities for validation as a Secured-Core offering. What does this include? It includes a validated set of hardware, firmware, and drivers that satisfy the security requirements. Therefore, when organizations purchase a Windows Server 2022 server certified as a Secured-Core offering, they can be confident it is certified using the standards outlined by Microsoft regarding the included components and software.
Advanced protection
Modern threats include very advanced attack techniques. Secured-Core includes advanced protection that is made up of both hardware and software solutions to counterattack these threats. These include:
-
- Hardware Trusted Platform Module 2.0 – provides a secure hardware store for storing sensitive information such as cryptographic keys and data. It also holds a “fingerprint” of sorts for the boot components. If the fingerprint of the boot components changes, it can identify if this is tampering. It also bolsters the protection provided by BitLocker.
-
- Protected Firmware – Firmware has become increasingly vulnerable to malware and ransomware. Secured-Core provides capabilities such as Dynamic Root of Trust of Measurement technology (DRTM) and DMA protection
-
- Virtualization-based Security (VBS) – Secured-Core supports the implementation of VBS and hypervisor-assisted code integrity checks (HVCI). Using VBS, customers can also use new technologies such as Credential Guard, which helps protect against stolen credentials.
Preventative defense
Today’s security solutions must be proactive and not reactive to stay ahead of modern threats and techniques used by hackers. The capabilities provided by the Secured-Core offering in Windows Server 2022 dramatically increase the tools IT admins and SecOps have to defend against the modern threat landscape.
Windows Server Secured-Core checks scan for the following specific features enabled with a fully implemented Secured-Core deployment in Windows Server 2022. If you use Windows Admin Center to view Secured-Core components (as we will see below), it shows the following checks in Secured-Core deployment:
-
- HVCI
-
- Boot DMA Protection
-
- System Guard
-
- Secure Boot
-
- VBS
-
- TPM 2.0
Let’s consider these in more detail.
HVCI
Hypervisor Enforced Code Integrity (HVCI) works in tandem with Virtualization Based Security (VBS) to protect Windows Server and client operating systems from drivers that are bad, malicious, or otherwise insecure as well as malicious system files. Specifically, it helps prevent tampering with Control Flow Guard (CFG) and ensures valid certificates for security-related processes such as Credential Guard.
Boot DMA Protection
Boot DMA Protection helps to protect Windows Server and client operating systems from drive-by Direct-Memory Access attacks. These attacks can occur using PCI hotplug devices connected to externally accessible PCIe ports and internal PCIe ports.
A successful drive-by DMA attack can lead to sensitive information being disclosed or even malware injection leading to bypassing the lock screen or remote controlling the node. With the Boot DMA Protection enabled, Windows can block external peripherals from staring and performing DMA unless the drivers support memory isolation.
System Guard
System Guard is part of the Microsoft Windows Defender solution. As the name implies, System Guard guards the system and maintains the integrity of the system during the boot process. In addition, it works to validate that system integrity has not changed through local and remote attestation.
System Guard helps to defend end-user PCs against the types of rootkits and bootkits that commonly affected Windows 7 systems. With Windows 7, malicious software could start before Windows starts, which allowed it to run with the highest privileges. With modern hardware and operating systems such as Windows Server 2022, System Guard protects against these kinds of bootkits and prevents any unauthorized firmware or software from launching before the Windows bootloader.

Windows Defender System Guard Overview
Secure Boot
Secure Boot is not a Microsoft solution or technology. Instead, the PC industry developed it to help make sure a device boots with software validated and trusted by the OEM hardware vendor. By checking each boot software signature, including UEFI firmware drivers, Secure Boot makes sure the signatures are valid and authorized. It helps to validate the software has not been tampered with by an attacker.
Virtualization-based Security (VBS)
As part of the Secured-Core components, Windows Server 2022 contains Virtualization-based Security (VBS). With Virtualization-based Security (VBS), hardware virtualization is used to create a specialized secure region of memory isolated from the operating system. Windows can access the secure virtual mode for security-related tasks. It includes increasing OS protection from vulnerabilities and preventing malicious code that attempts to defeat protective mechanisms.
As mentioned earlier, HVCI makes use of VBS to strengthen code integrity enforcement. VBS makes use of the Windows Hyper-V hypervisor for the virtual secure mode used to enforce restrictions to protect crucial system and OS resources. An example includes authenticated user credentials by way of the Credential Guard solution that makes use of VBS.
TPM 2.0
The Trusted Platform Module is a hardware technology designed for security-related functions. The TPM chip contains a crypto-processor that allows generating, storing, and limiting the use of cryptographic keys. These generally include features that help to ensure it is tamper-resistant so that malicious software cannot tamper with the security-enabled functions of the TPM chip. TPM 2.0 contains many new hash algorithms and security features compared to the TPM 1.2 standard. Windows Server 2022 can take full advantage of the features and capabilities found in the TPM 2.0 module.
Simplified Configuration Tools
Microsoft has been feverishly working on a new tool since Windows Server 2019 for server configuration and management. This new tool is Windows Admin Center which is the new way forward for managing Microsoft Windows Server. It replaces the old Server Management console, even though the Server Management tool is still in Windows Server 2022.
A tough challenge with security is ensuring that configurations are implemented correctly and consistently. When configuration tooling is challenging to use or includes many different tools and dashboards required to implement various configuration parts, it can lead to implementation gaps. Any gap in security or insecure configuration leading to vulnerabilities is a serious issue.
Windows Admin Center provides a single-pane-of-glass interface that businesses can use to implement Windows Server configurations across the board, including the Security dashboard. This capability has been missing in legacy tools, and consoles such as Server Manager found in Windows Server 2019. In addition, the new Windows Admin Center compliments the implementation of Secured-Core security configurations by giving visibility to this in the Windows Admin Center UI.
As a note, the Secured-Core dashboard in Windows Server 2022 is still in Preview release at the time of this writing. To access the Secured-Core functionality in Windows Admin Center, you need to enable the Insider Preview “feed” in Windows Admin Center. To add the Insiders Preview feed so you can get the latest Insider Preview extensions available in Windows Admin Center, navigate to Settings using the settings cog in the upper right-hand corner. Click the Extensions > Feeds tab. Navigate to the Add button and click. Enter the feed URL: https://aka.ms/wac-insiders-feed

Adding the Insider Preview feed for Windows Admin Center
After adding the Insider Preview feed in Windows Admin Center, you will see a new, higher versioned, Security extension. At the time of writing, the version installed was 0.23.0.

Installing the Insider Preview Security Extension
After installing the Insider Preview Security extension, IT admins will have access to a new tab that displays on the Security dashboard, called Secured-Core.
It provides strong visual cues on which features are enabled or not configured or supported.

Viewing Secured-Core configuration using Windows Admin Center
Microsoft has built-in the capability to enable and disable the Secured-Core features from the Windows Admin Center dashboard. This feature makes controlling the Secured-Core features easy to configure and audit. Notice below. The HVCI feature has been enabled from the Windows Admin Center dashboard. The Windows Server 2022 server is now prompting a reboot.

Enabling and Disabling Secured-Core features from Windows Admin Center
The Security dashboard also gives visibility to and allows configuration of the Virus & threat protection configuration and scans leveraging Windows Defender. You can also view Protection history for events and default actions.

Configuring Virus & threat protection with Windows Admin Center
Secure Connectivity
An area that has been dramatically improved with Windows Server 2022 is secure connectivity. What improvements have been made in terms of connectivity with Windows Server 2022? Let’s consider the following:
-
- Secure protocols by default
-
- Secure DNS
-
- Server Message Block (SMB) improvements
Secure protocols by default
When it comes to connectivity protocols, some protocols are more secure than others. Therefore, when hardening for security, insecure protocols need to be disabled, and businesses must make sure they are using the latest and most secure protocols for network transmissions.
Windows Server 2022 takes the heavy lifting out of this effort. It contains the most secure version of HTTPS enabled by default, TSL 1.3. It helps protect clients’ data connecting to the server and eliminates obsolete and insecure cryptographic algorithms. In addition, Windows Server 2022, using the latest standards, encrypts as much of the handshake as possible.
Secure DNS
Windows Server 2022 improves DNS security by implementing what is known as DNS-over-HTTPS (DoH). DNS-over-HTTPS encrypts DNS queries made over the HTTPS protocol. It dramatically enhances DNS security by keeping DNS queries private. In addition, it helps to prevent malicious eavesdropping of traffic and DNS data manipulation.
Server Message Block (SMB) improvements
Server Message Block (SMB) is at the heart of Windows Server file copies. Windows Server 2022 provides the latest and most significant improvements to the SMB protocol. Windows Server 2022 now supports encrypting SMB traffic with the latest cryptographic suites, including AES-256-GCM and AES-256-CCM. In addition, Windows Server 2022 will automatically negotiate the highest possible encryption suite when clients support the higher level of encrypted communications. These settings can also be configured using Group Policy.
Another interesting security improvement with SMB encryption is SMB East-West encryption of storage communications for Cluster Shared Volumes (CSVs). Using Storage Spaces Direct (S2D), you can encrypt or sign east-west intra-cluster communications for security purposes.
A new feature is SMB over QUIC, an enhancement of SMB 3.1.1 in Windows Server 2022 Datacenter: Azure Edition. It allows using the QUIC protocol instead of TCP. In addition, using SMB over QUIC with TLS 1.3 eliminates the need for VPN to access file servers over SMB when using Windows.
Hybrid Management Tools
Microsoft has built a solid set of hybrid features into the Windows Server platform, starting with Windows Server 2016 and moving forward. Windows Server 2019 greatly improved on the native hybrid features built into the operating system. Windows Server 2022 takes to the next level of hybrid capabilities. Why is hybrid management crucial for today’s businesses and, particularly, their security initiatives.
Most businesses today are using infrastructure that is housed both on-premises and in the cloud. This infrastructure layout is known as a hybrid configuration. As many organizations are required to keep a subset of infrastructure locally housed in their own physical on-premises data centers for compliance and other reasons, the hybrid world of infrastructure is no doubt here to stay for the foreseeable future.
As infrastructure spans between on-premises data centers and cloud environments such as Microsoft Azure, it becomes even more critical for businesses to focus on security between the two. Historically, it has been challenging to standardize security and management tools between on-premises and cloud environments as each has its specific tooling, processes, dashboards, configuration possibilities, etc.
With Microsoft Azure and modern Windows Server operating systems such as Windows Server 2022, Microsoft has created a solution to help remedy management disparities between the cloud and on-premises Windows Server instances. Azure Arc is a Microsoft Azure solution that allows the onboarding of on-premises Windows Servers into the management plane of your Microsoft Azure account, bringing on-premises resources under the purview of Azure Resource Manager (ARM).
Specifically, Azure Arc provides simplified management across many environments maintained by many organizations today, including Windows, Linux SQL, and even Kubernetes clusters across data centers and geographic locations. So what can you do with Azure Arc?
-
- Provide centralized management of resources, both in Azure and on-premises
-
- Gain centralized visibility in the Azure portal of both Azure and on-premises resources
-
- Apply compliance and governance standards across all environments in a standardized way
-
- Provide access delegation to resources using the role-based access control (RBAC) features in Azure
-
- Gain organization and inventory benefits as you can house objects from Azure or on-premises locations into management groups, subscriptions, resource groups, in addition to using tagging

Azure Arc dashboard in the Azure portal
Azure Security Center is another offering from Microsoft, centred around security, that helps unify infrastructure security management and provide a consistent set of tools and security policies, regardless of whether resources exist in Azure or on-premises. It is built seamlessly into Windows Admin Center. In addition, you can sign in to Azure and onboard into the service directly from the tool.
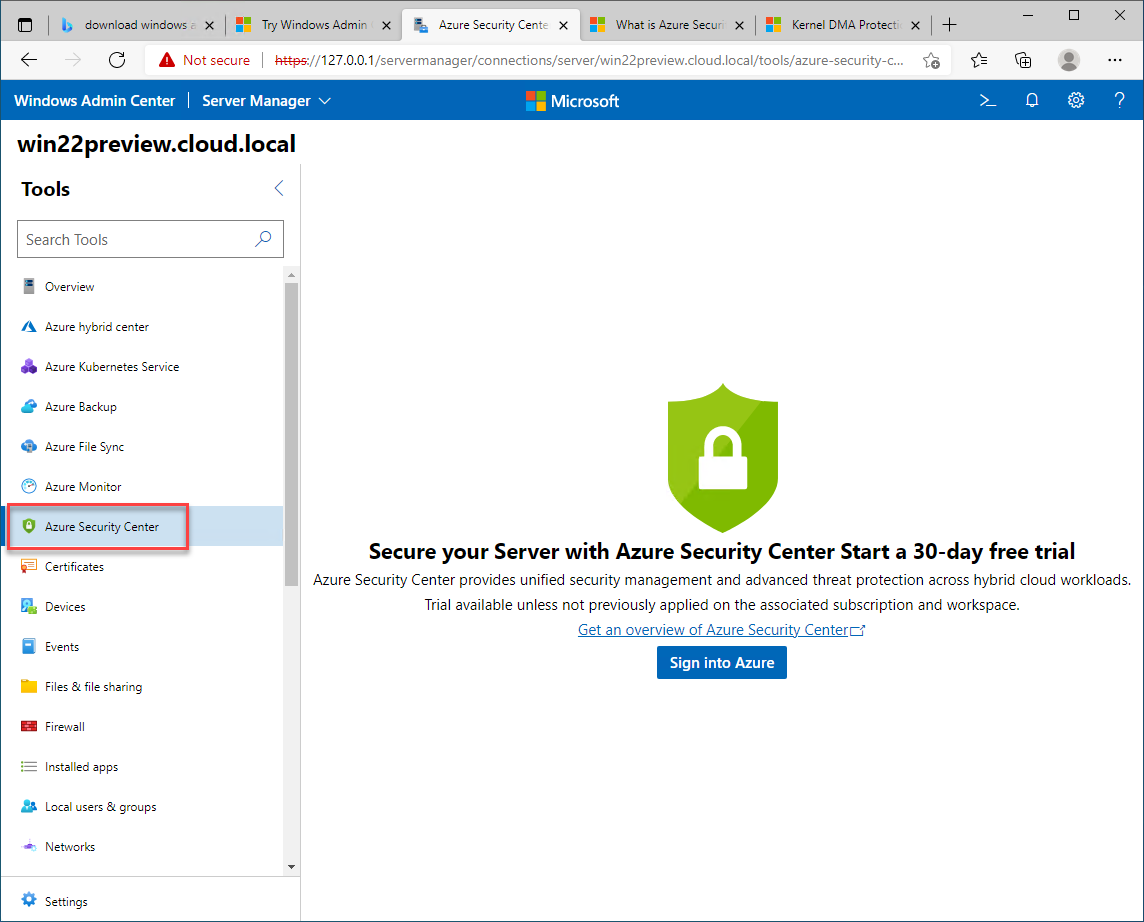
Launching the Azure Security Center dashboard from Windows Admin Center
It helps businesses carry out the following Windows Server 2022 security-related tasks:
-
- Manage organization security policy and compliance
-
- Perform continuous assessments
-
- Build network maps
-
- Configure best practices and recommended controls
-
- Protect against threats

Azure Security Center provides a consistent view of the security of on-premises and cloud workloads
Another great feature extended to Windows Server 2022 is the Azure hybrid center available directly from Windows Admin Center. With Azure hybrid services, IT admins can:
-
- Protect virtual machines
-
- Extend on-premises storage capacity and compute resources in Azure
-
- Simplify network connectivity
-
- Centralize monitoring, governance, configuration, and security

Available hybrid services with Windows Server 2022 and Microsoft Azure
Connecting your on-premises Windows Server 2022 server to the Azure hybrid center is as easy as registering your Windows Admin Center gateway server and signing in to your Azure portal.

Azure hybrid center available from Windows Admin Center
Windows Server 2022 Azure Edition Hotpatching
Microsoft has introduced a new patching technology that is part of the Azure Automanage platform in Microsoft Azure. It works with the “Azure Edition” of Windows Server products. Hotpatch is supported in Windows Server 2022: Azure Edition and is a new way of installing Windows updates in Windows Server Azure Edition virtual machines that do not require a reboot after installation.
The hotpatching feature drastically reduces maintenance windows and the downtime associated with the typical installation of Windows Updates in Windows Server. Hotpatch first establishes a baseline of the Windows Update Latest Cumulative Update. Hotpatches are then periodically released and contain updates that don’t require a reboot. Planned baselines are released on a regular cadence interval with hotpatch releases in between. In addition, unplanned baselines are released in case of emergency security patches and if the patch can’t be released in a hotpatch.
Customers making use of Windows Server 2022: Azure Edition in their Azure environment can take advantage of the latest enhancements and implementations of the hotpatch feature using Azure Automanage.
The Future of Windows Server Security
There are a large number of new features contained in Windows Server 2022. It represents the latest capabilities and features provided by Microsoft for the Windows Server platform. In addition, many enhancements are security-related and help customers with their cybersecurity posture, both on-premises and in the cloud.
As shown, Microsoft has worked hard to provide better tools for managing Windows Server 2022. For example, Windows Admin Center provides a single-pane-of-glass tool that perfectly compliments the new features and capabilities in Windows Server 2022. While many of the dashboards are still in preview, it helps to see the direction Microsoft is headed with an all-inclusive solution to standardize management of both on-premises and cloud resources seamlessly.
The Secured-Core functionality made possible by Windows Server 2022 and the Windows Admin Center management console allows customers to easily provide the core security fundamentals to their Windows Server environment powered by Windows Server 2022. Windows Server 2022 also provides the latest standards and implementations of secure protocols such as TLS 1.3 and SMB encryption.
In addition, using Windows Admin Center provides the gateway to integrating on-premises Windows Server installations with Azure. There are strong hybrid integration capabilities found in Windows Admin Center. It allows integrating your on-premises Windows Server 2022 installations into Azure with only a few clicks and signing in to your Azure account. All of these features make Windows Server 2022 the most secure Windows Server operating system released to date.


Not a DOJO Member yet?
Join thousands of other IT pros and receive a weekly roundup email with the latest content & updates!









