Save to My DOJO
Table of contents
It’s no secret that Microsoft invests a lot in security solutions and that platforms like Microsoft 365 and Azure provide a rich set of tools for securing your business.
At Ignite 2020 Microsoft announced some new capabilities and more importantly, a rename of most tools, making what was already a confusing line-up even more confounding. In this article, we’ll cover new features and the new names and where the tools fit into the overall security posture of your company.
You may have heard of Endpoint Detection and Response (EDR), now Microsoft (the marketing department?) is extending this term to Extended Detection and Response (XDR). And there are two newly named services, Microsoft 365 Defender and Azure Defender that provide XDR capabilities.
Before we continue, if you haven’t already signed up to our webinar on October 7 How to Fortify your Business with Azure Active Directory, do that now. I will be presenting that event along with longtime Altaro presenter Andy Syrewicze and we’ve got some really great content lined up for anyone who manages Microsoft-based cloud infrastructure accessed by multiple users. The threats to your data are growing, make sure you’re prepared – save your seat now!
Microsoft 365 Defender
In this family, you’ll find Microsoft Defender for Endpoint (formerly known as Microsoft Defender Advanced Threat Protection). If you’re not familiar with it, this is not your father’s Windows Defender basic Antivirus from Windows 7, this is a comprehensive EDR (XDR now?) tool, using Machine Learning both on the endpoint and in the cloud to identify, mitigate and remediate threats across Windows, MacOS and Linux. The Android agent that was in preview is now Generally Available and there’s a new iOS agent (for 11.0+) in preview.
Microsoft 365 Defender (courtesy of Microsoft)
Here’s also Microsoft Defender for Office 365 (previously Office 365 Advanced Threat Protection), an extra protection on top of the standard Exchange Online Protection. This opens and scans unknown and potentially malicious attachments in a VM before delivering it to an end-users inbox as well as rewrites and scans URL links in emails, Teams and SharePoint / OneDrive for Business before users are allowed access to the site or document.
The third sibling is Microsoft Defender for Identity (the artist formerly known as Azure Advanced Threat Protection), a tool focused on your on-premises Active Directory and detecting attackers as they infiltrate, move laterally and elevate their privileges.
Finally, the central console known as Microsoft Threat Protection has been renamed to Microsoft 365 Defender.
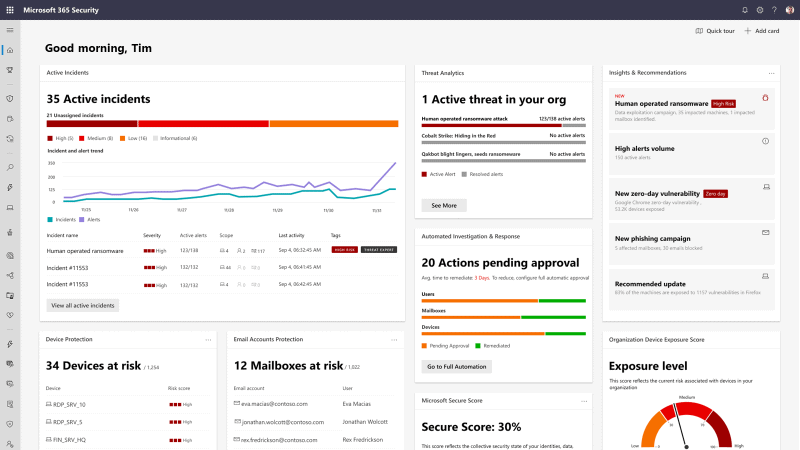
Azure Defender
This is also an amalgamation of existing products and services with some new features. We’ve had Azure Security Center for some years now and it’s grown in capabilities and scope and it’s been renamed to Azure Defender for Servers, together with Azure Defender for IoT (Azure Security Center for IoT) and Azure Defender for SQL (formerly Advanced Threat Protection for SQL).
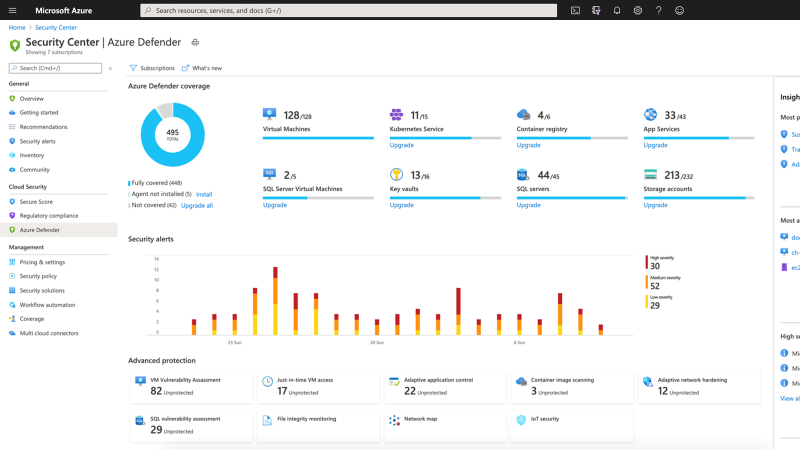
Azure Defender (courtesy of Microsoft)
Azure Defender has a new feature that shows you at a glance which resources are protected, and which need protection, as well as offering protection for SQL servers on-premises and in other clouds. There’s also Kubernetes policy management and scanning of container images in registries.
The recent acquisition of CyberX is also integrated into Azure Defender to cater for existing (read “non-secure”) Operational Technology deployments.
Azure Sentinel
This cloud-based SIEM didn’t get a rename (thank you Microsoft – I really like this name) but as a tool that ingests and analyses all your security log data, it’s vital to the overall security story. There are new features added all the time to Sentinel but noteworthy additions released at Ignite is User and Entity Behavior Analytics (UEBA)– tracking what’s “normal” for a user account or device and flagging abnormal actions.
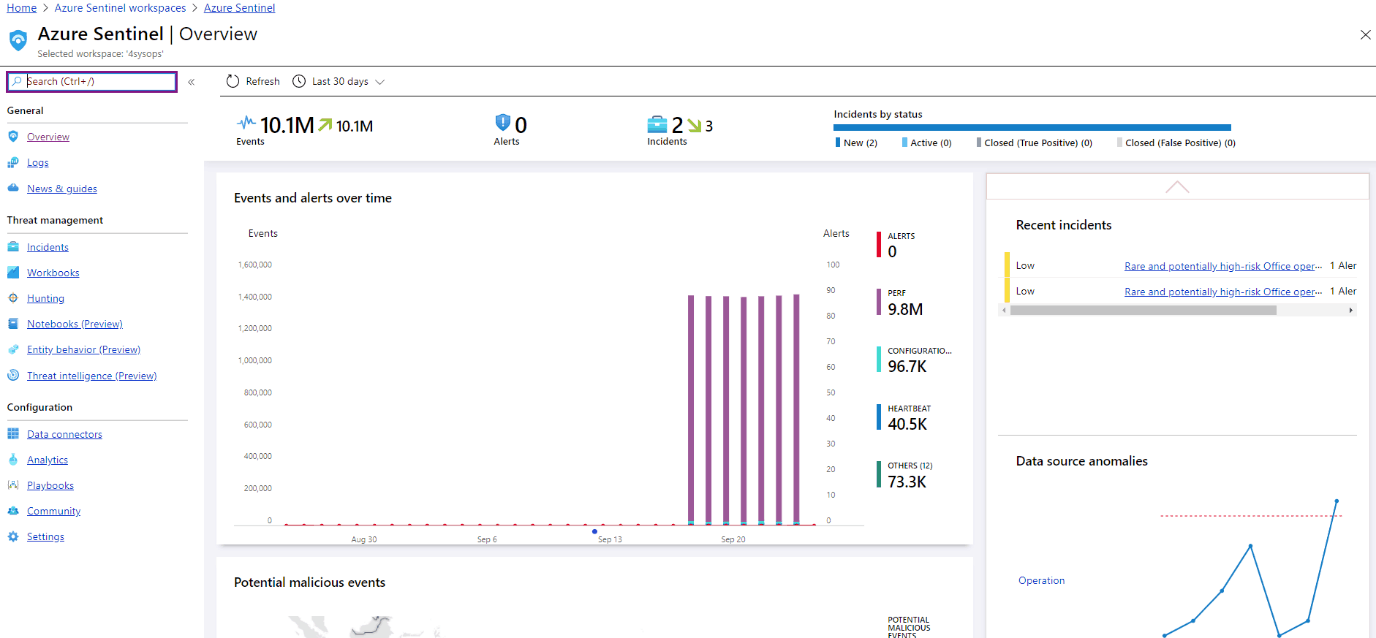
Sentinel Portal
Ingesting Threat Intelligence (TI) in Sentinel has been a bit clunky up until now, a new blade lets analysts view, filter, tag and search indicators that are imported from TI providers.
Correlating security events and alerts with other data sources (asset inventory, employees that have left for instance) used to be a manual process, the new Watchlist feature lets you use imported CSV data in rules, workbooks and notebooks. Speaking of notebooks, they’re now extended into Azure Machine Learning as a platform, giving you the full Jupyter experience plus configurable compute options. For customers with in-house expertise, you can also build your own Machine Learning models for Sentinel.
Conclusion
I note that Cloud App Security hasn’t been herded into one of these two new families and I’m wondering where this cloud-based CASB is going to land.
Apart from the obvious confusion that’s going to arise as we all get used to the new names, I think this is a good move. It consolidates the different tools and clarifies how they all fit together towards the ultimate goal – keeping your business out of the courtroom and out of the papers.
[thrive_leads id=’18633′]


Not a DOJO Member yet?
Join thousands of other IT pros and receive a weekly roundup email with the latest content & updates!