Save to My DOJO
As an IT Professional, you might find yourself blessed with the unfortunate scenario of working on a Hyper-V server that is not able to authenticate to the domain and the cached domain credentials are no longer working. In addition to this predicament, you learn that there is no documentation for the local administrator password. Either the client who you’re working for doesn’t know the local administrator password or the previous engineer who built the server is no longer working for your company and the standard passwords aren’t working. A 3rd party password cracker application will allow you to reset the local administrator password. The drawback is you have to pay for it and in my experience they don’t always work. Follow the steps below and use the Ease of Access Exploit to change the local administrator password.
The Ease of Access Exploit modifies the windows system files to enable you to open a command prompt at the windows login screen. This command prompt also runs as the system account, allowing you to add, create, or edit local accounts. The only tool needed for this exploit is a Windows CD. It can be a Windows Vista, Windows 7, Windows 8, Server 2008 R2, Server 2008, Server 2012 or a Server 2012 R2 CD. Even though a Windows Server 2008 CD is used in this example, Linux distributions and Ultimate Boot CD will also work as well. The commands would be the same; the only difference would be the way you get to the command prompt.
How to reset your admin password
To get started, boot the server to a Windows CD. Browse to the repair section and open up the command line tool.
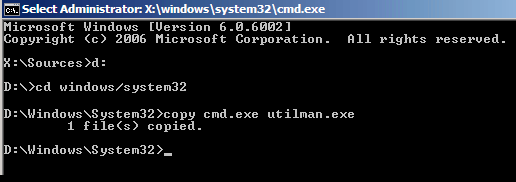
Inside the command line, change directories to the windows installation directory. It will usually be the C, D, or E drive. In this example the D drive contains the Windows system files. Type the following commands:
D:
Cd Windows/system32
Ren utilman.exe utilman.exe.old
Copy cmd.exe utilman.exe
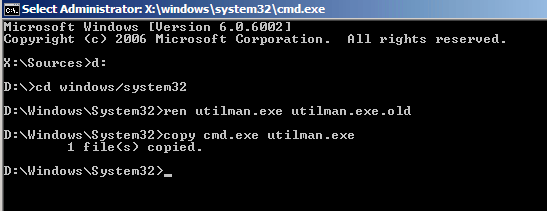
This will change directories to the system32 directory and rename the Utilman.exe file, which is the executable file that allows users to open up the Ease of Access menu. This menu allows users to modify the contrast of the screen and access features such as the Magnifier and Narrator. After renaming the utilman.exe file, cmd.exe is copied and renamed as “utilman.exe”. Now when users click on the ease of access tool at the windows login, the command prompt will appear instead of the normal menu.
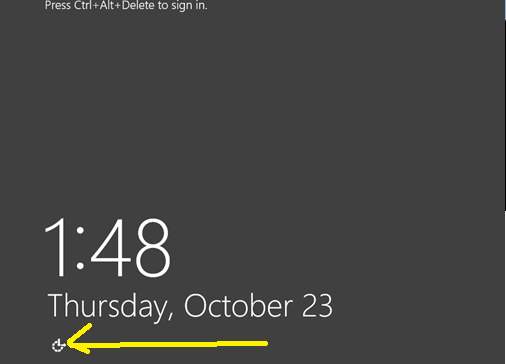
Reboot the host and start up normally. At the login screen click on the ease of access button in the lower left corner. A command prompt running as the system account will appear.
Now you can either enable and reset the local administrator password or create an additional account and add it to the local administrators group.
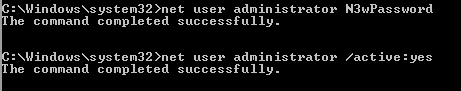
Change the Local Administrator Password
Type the following commands to change the local administrator password and enable the account if it’s disabled:
Net user administrator newpassword
Net user Administrator /active:yes
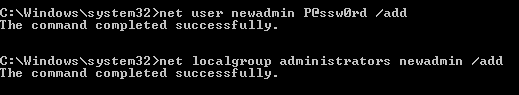
Create an Additional Local Administrator Account
Type the following commands add another local administrator account
Net user newadmin P@ssw0rd /add
Net localgroup administrators newadmin /add
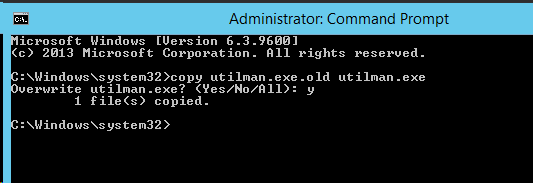
You can now login to the server with the new local administrator password or with an additional admin account. Once logged in, make sure to revert the Ease of Access menu back to normal by typing the following commands:
Copy utilman.exe.old utilman.exe
What if I Am Using Windows Server Core?
Windows server core is an installation option that is available during the initial install of Windows Server 2008 and higher. Essentially this will install windows without the graphical user interface. Read “Benefits of a Windows Server 2012 R2 Core Installation” by Andy Syrewicze for more information on why Server Core should be used. The Utilman.exe file is not included in the install of server core. So when you boot to the windows CD you can skip the part where you back up the utilman.exe executable. Type in the following commands:
D:
Cd Windows/system32
Copy cmd.exe utilman.exe
This will copy the command line executable and rename it as the utilman.exe file. When the host is rebooted, it will think the utilman.exe file exists and the Ease of Access button will respond by opening the command prompt when clicked on.
How Do I Protect My Server Against This Exploit?
The easiest and most inexpensive way to protect against this exploit is to set a BIOS password on the Hyper-V host and change the boot order to exclude CD-ROMs and USB drives. This would protect against an internal attacker that compromises the out-of-band management utility on the host. However, if the attacker gains physical access to the server, they can reset the BIOS password and still use this exploit. This is why access to the server room should always be secured. For more information on securing Hyper-V, be sure to check out “7 Keys to Hyper-V Security” by Eric Siron.


Not a DOJO Member yet?
Join thousands of other IT pros and receive a weekly roundup email with the latest content & updates!









77 thoughts on "How to Reset A Forgotten Hyper-V Admin Password with a Windows CD"
OMG, thank you!
I my company they locked themselves out of a server and couldn’t find the backups.
This little workaround with the command line saved my work from a few weeks.
OMG, thank you!
I my company they locked themselves out of a server and couldn’t find the backups.
This little workaround with the command line saved my work from a few weeks.
I usually use PCUnlocker for resetting a lost password. Just a few minutes ago I tried your trick and it worked great! Thanks for sharing!
That was easy. Thanks man.
Thank you .. that was helpful, saved lot of time for me
It’s lot of help me to creating to new password since i forgot my password. Thanks you.
Works perfectly .. we had a development HV machine in which the last resource left and none of his passwords worked for us .. and we used this trick to gain access back to the machine that contains all the code ..
Great, we are glad this worked for you Sam!
Didn’t work for me on a hyper-v 2016 core machine. I copied cmd.exe to utilman.exe but no Ease of Access button appeared.
However, I followed the following similar steps:
1. Boot from the HyperV USB
2. Shift F10 to open command prompt
3. change to D:windowssystem32
3. Rename logonui.exe
4. Copy cmd.exe to logonui.exe
5. reboot to the operating system which then opens a cmd prompt, ignore he access errors
6. type “net user administrator newpassword”
7. boot from the HyperV usb stick
8. Shift F10 to command prompt
9. Copy the original logonui.exe (step 3) back to replace the one created in step 4.
10. Reboot and you can log into the machine
Hi Kevin,
You are correct, from Windows 2016 onwards Microsoft “fixed” the utilman.exe issue. I’m glad you found and shared an alternative workaround.
Paul Schnackenburg, Altaro DOJO Technical Editor