Save to My DOJO
Personally, I find Microsoft’s recent moves to improve support for Linux and its overall relationship with open source to be very exciting, including Kali Linux Hyper-V installations. I’ve taken full advantage of these new opportunities to rekindle my love for the C and C++ languages and to explore Linux anew. Since my general line of work keeps me focused on the datacenter, I’ve similarly kept tight focus on server Linux builds and within the confines of Microsoft’s support matrix. Sure, I’ve had a good time learning other distributions and comparing them to what I know. But, I also realize that I’ve been restricting myself to the safe walled garden of enterprise-style deployments. It’s time for something new. For my first step outside the walls, I’m going to take a crack at Kali Linux on Hyper-V and see how to get this very popular security tool running inside a Hyper-V environment.
What is Kali Linux?
The Kali Linux project focuses on security. In most of the introductory literature, you’ll find many references to “penetration testing”. With a bit of searching, you’ll find a plethora of guides on using Kali to test the strength of your Windows computers.
The distribution itself is based on Debian. Truthfully, even though I’d like to tell you that we’re going to stray far, far away from the beaten path, we won’t. Almost no one picks up a copy of the Linux kernel and builds an all-new distribution around it. Nearly every maintained distribution connects somewhere into the general distribution categories on Microsoft’s list. Anything else falls under the category of a “source-based” distribution (like Gentoo). I’d need to drastically improve my Linux knowledge to help anyone with one of those.
Why use Kali Linux?
The distributions that I tend to cover in these articles fall best under the category of “general purpose”. In that respect, they have much in common with Windows and Windows Server. You stand up the operating system first, then install whatever applications and servers you need it to operate or provide. Web, DNS, storage, games — anything goes.
Kali Linux has a purpose. You could use it as a general purpose platform, if you want. That’s not an optimal use of the distribution, though. Kali is designed to probe the strength of your environment’s computer security. During install, there won’t be any screens asking you to pick the packages you want to install. You won’t get an opportunity to tick off boxes for LAMP or DNS servers. If you want those things, look at other distributions. Kalix Linux is here to pentest, not hand out IP addresses. Err… well… I guess rogue DHCP qualifies as security testing… But, you get the idea.
A natural question, then, is, “So, Eric, what do you know about pentesting?” The answer is: very little. Where I work, we have a security team. I can notify them when I build a new system, and they’ll test it and send me a report. I accept that I will never rise to expert level, if for no other reason than because I don’t have the time. Still, I should know more than I do. Many seasoned sysadmins would be surprised at how easily an attacker can break into a system set at defaults. Since the people behind the Kali Linux project have done all the work to make a convenient entry point, I’m going to take advantage of it. I recommend that you do the same.
Why Use Client Hyper-V for Kali Linux?
I won’t tell you why you should use a Microsoft hypervisor as opposed to some other hypervisor. I use Microsoft platforms and services for almost every aspect of my home and work computing, so my natural choice is to stick with it. If your story is different, then stay with what you know.
I will tell you that Client Hyper-V makes more sense than server Hyper-V for Kali Linux Hyper-V. I’ll make an exception for those of you that run Windows Server as your primary desktop. That’s not a thing that I would do, but hey, no judgment here.
Why I use Kali Linux under Client Hyper-V:
- Kali Linux Hyper-V is best used interactively with a desktop interface. If I were to run Kali from within my datacenter, I’d need to use VMConnect against a remote host. I’ve never liked that. So, my choice here for Hyper-V Kali Linux again is client Hyper-V.
- Most attacks won’t come from within the datacenter, so why would your primary penetration testing tool live there? Put it into a user network. Run it from a computer that can access your wired and wireless networks.
- Kali Linux Hyper-V allows you to perform all sorts of spoofing quickly and easily. You can flip MACs and hop networks in moments. You can hide Kali behind NAT to fool many network access protection schemes and then, within seconds, drop it on the network alongside my host OS.
- I don’t want to replace my primary desktop. I don’t necessarily need to use any hypervisor; I could just install Kali right to my desktop. I could stand up a second physical machine right next to me and use Kali on that. But, this is the sort of thing that hypervisors were built for; more computers in less space, so Kali Linux Hyper-V it is. I can keep my general purpose desktop and have the special-purpose Kali running happily together.
So, let’s look at how to install Kali Linux on Windows 10 Hyper-V. As we will cover, a Kali Linux Hyper-V environment is easily provisioned.
Download Kali Linux for Hyper-V
As a side effect of having a specific purpose, Kali Linux does not provide many install flavors. Start at the Kali Linux homepage. Click the Downloads header at the top of the page. Behold — the list. It looks long, but there’s really not that much there. You’re mostly picking the bitness (most are 64-bit) and the user interface experience that suits you. Note – there is no specific Kali Linux Hyper-V image download available, such as a prebuilt VHD/VHDX disk. So, the Kali Linux ISO Hyper-V installation is the way to go.
This article uses the standard 64-bit distribution of Kali Linux 2017.1. However, the latest release of Kali Linux currently is 2022.1. If you choose something else, your experience may be different. Overall, the general installation process will be similar.
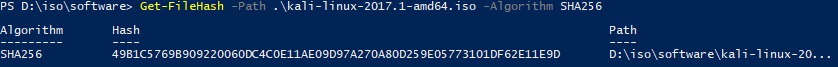
Verifying the ISO File Hash
Since we’re talking security, let’s start by verifying our file. On the Kali download page, next to the file link, you’ll find its SHA256 hash:
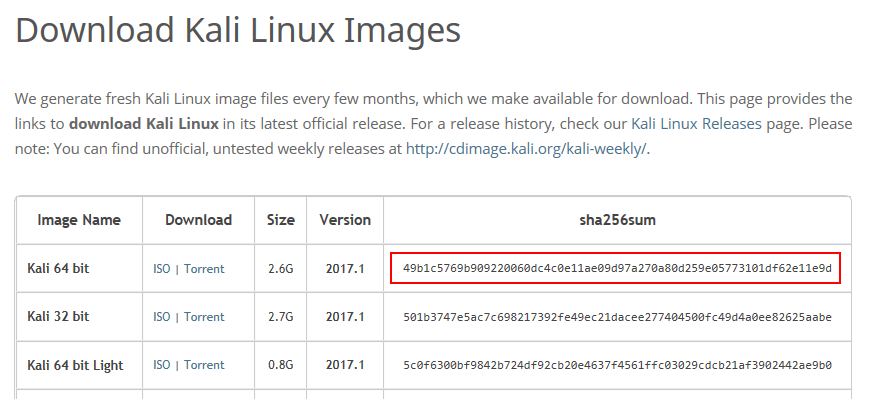 (source: https://www.kali.org/downloads/, as of June 17th, 2017)
(source: https://www.kali.org/downloads/, as of June 17th, 2017)
Use PowerShell to determine the hash:
Get-FileHash -Path .kali-linux-2017.1-amd64.iso -Algorithm SHA256
You’ll get output that looks like the following:
If you’re OK with “good enough”, you can do a quick ‘n’ dirty eye scan — basically, just visually verify that the codes look more or less the same. Even minor changes to a file will throw off the hash substantially. But, it’s not impossible to have two files with a similar hash. And, since we’re talking security, trust no one.
In your PowerShell prompt, do exactly this:
- Ensure that you are at the beginning of a new command line; no text entered, just a prompt.
- Type a single quote mark: ‘
- Use the mouse to highlight the Hash output from the previous command. Press [Enter] to put it on the clipboard. Right-click to paste. That should place the code immediately after the single quote.
- Type another single quote mark to close off the file hash.
- Enter a space, then -match, then another space.
- Type another single quote mark to start a new string.
- Highlight the corresponding hash code on the Kali download page. Switch back to the PowerShell prompt and right-click to paste it.
- Type another single quote mark to close off the published hash.
- Press [Enter].
This is what you should see (with possibly different hash values):
If you get an error, check your input. If you get False, check your input. If the input is OK, then your file does not match the expected hash. Most likely, the download corrupted. Maybe somebody hijacked it. Either way, get another.
Installing Kali Linux as a Guest in Client Hyper-V
On to the good stuff!
Creating a Hyper-V Virtual Machine for Kali Linux
I do not mean for this article to be a tutorial on creating VMs in Client Hyper-V. I assume that you know how to create a virtual machine, attach an ISO to it, start it up, and connect to its console.
I have a script that I use to create Linux VMs. The more I use it, the more deficiencies I notice. I will someday make this script better. Here’s what I currently have:
#function New-LinuxVM {
#requires -Modules Hyper-V
[CmdletBinding(SupportsShouldProcess=$true)]
param
(
[Parameter(Mandatory=$true, Position=1)][String]$VMName,
[Parameter()][String]$VHDXName = '',
[Parameter()][String]$VMStoragePath = '',
[Parameter()][String]$VHDStoragePath = '',
[Parameter()][String]$InstallISOPath = '',
[Parameter()][Switch]$Cluster,
[Parameter()][String]$VMSwitchName = '',
[Parameter()][uint64]$StartupMemory = 512MB,
[Parameter()][uint64]$MinimumMemory = 256MB,
[Parameter()][uint64]$MaximumMemory = 1GB,
[Parameter()][uint64]$VHDXSizeBytes = 40GB
)
if([String]::IsNullOrEmpty($VHDXName))
{
$VHDXName = '{0}.vhdx' -f $VMName
}
if($VHDXName -notmatch '.vhdx$')
{
$VHDXName += '.vhdx'
}
if([String]::IsNullOrEmpty($VMStoragePath))
{
$VMStoragePath = (Get-VMHost).VirtualMachinePath
}
if(-not (Test-Path -Path $VMStoragePath))
{
Write-Error -Message ('VM path {0} does not exist.' -f $VMStoragePath)
return
}
if([String]::IsNullOrEmpty($VHDStoragePath))
{
$VHDStoragePath = (Get-VMHost).VirtualHardDiskPath
}
if(-not (Test-Path -Path $VHDStoragePath))
{
Write-Error -Message ('Storage path {0} does not exist.' -f $VHDStoragePath)
return
}
$VHDStoragePath = Join-Path -Path $VHDStoragePath -ChildPath $VHDXName
if([String]::IsNullOrEmpty($InstallISOPath) -or -not (Test-Path -Path $InstallISOPath -PathType Leaf))
{
Write-Error -Message ('ISO {0} does not exist' -f $InstallISOPath)
return
}
if([String]::IsNullOrEmpty($VMSwitchName))
{
$VMSwitchName = (Get-VMSwitch | ? SwitchType -eq 'External')[0].Name
}
if([String]::IsNullOrEmpty($VMSwitchName))
{
Write-Error -Message ('No virtual switch specified')
return
}
$VM = New-VM -Name $VMName -MemoryStartupBytes $StartupMemory -SwitchName $VMSwitchName -Path $VMStoragePath -Generation 2 -NoVHD
Set-VMMemory -VM $VM -DynamicMemoryEnabled $true -MinimumBytes $MinimumMemory -MaximumBytes $MaximumMemory
Set-VMProcessor -VM $VM -Count 2
Start-VM -VM $VM
Stop-VM -VM $VM -Force
New-VHD -Path $VHDStoragePath -SizeBytes $VHDXSizeBytes -Dynamic -BlockSizeBytes 1MB
$VMVHD = Add-VMHardDiskDrive -VM $VM -ControllerType SCSI -ControllerNumber 0 -ControllerLocation 0 -Path $VHDStoragePath -Passthru
$VMDVDDrive = Add-VMDvdDrive -VM $VM -ControllerNumber 0 -ControllerLocation 1 -Passthru
$VMNetAdapter = Get-VMNetworkAdapter -VM $VM
Set-VMNetworkAdapter -VMNetworkAdapter $VMNetAdapter -StaticMacAddress ($VMNetAdapter.MacAddress)
Set-VMFirmware -VM $VM -BootOrder $VMDVDDrive, $VMVHD, $VMNetAdapter -EnableSecureBoot On -SecureBootTemplate 'MicrosoftUEFICertificateAuthority'
Set-VMDvdDrive -VMDvdDrive $VMDVDDrive -Path $InstallISOPath
if($Cluster)
{
Add-ClusterVirtualMachineRole -VMName $VMName
}
#}
This script creates a dynamically-expanding VHDX using a 1 megabyte block size, in accordance with Microsoft’s recommendation. A commenter on another of my Linux articles pointed out that the 1MB block size does not result in significant space savings on every Linux distribution. I have not tested the difference on Kali. It uses ext4, so I suspect that you’ll want the 1MB block size.
I used the script like this:
.New-LinuxVM.ps1 -VMName dtkali -VMStoragePath 'D:VMs' -VHDStoragePath 'D:VMsdtkaliVirtual Hard Disks' -InstallISOPath D:ISOsoftwarekali-linux-2017.1-amd64.iso -VMSwitchName vSwitch -StartupMemory 1GB -MinimumMemory 512MB -MaximumMemory 2GB -VHDXSizeBytes 100gb
It was necessary to pre-create the target VHDX path. That’s one of the deficiencies in the script. It’s also necessary to turn off Secure Boot after creation.
During use, I learned that Kali wants so much more memory than 2GB. These memory numbers are somewhat laughable. Be prepared to turn them up. It does seem to run well enough at 2GB, but I’m thinking that 4GB would be a more reasonable average running expectancy.
Installing Kali Linux from ISO
In case you missed it from the previous section: disable Secure Boot. Kali Linux Hyper-V does not include Kali’s boot signature. I did enable TPM support for it, but I don’t yet even know if Kali Linux Hyper-V will make use of it.
From here, I doubt that you really need much from me. Installation of Kali Linux Hyper-V is very straightforward. It shares one annoyance with Ubuntu: it has an obnoxious number of input screens broken up by long file operations, rather than cohesive input gathering followed by completion operations.
An installation walkthrough:
- You’re given many options right from the start. I simply chose to Start installer:
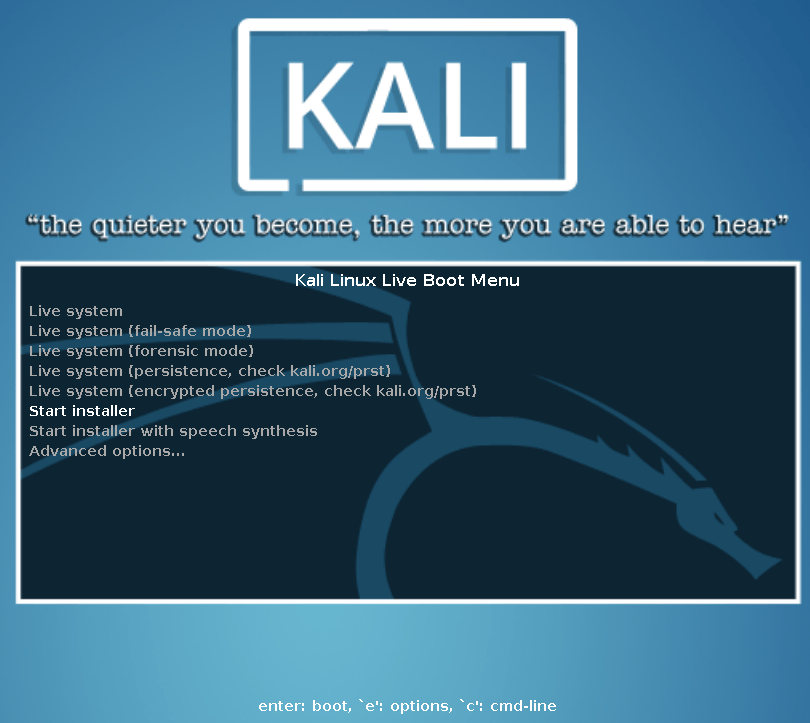 Note that several errors regarding not being able to find anything on SDA will scroll by; don’t worry about them. That’s normal for an empty disk.
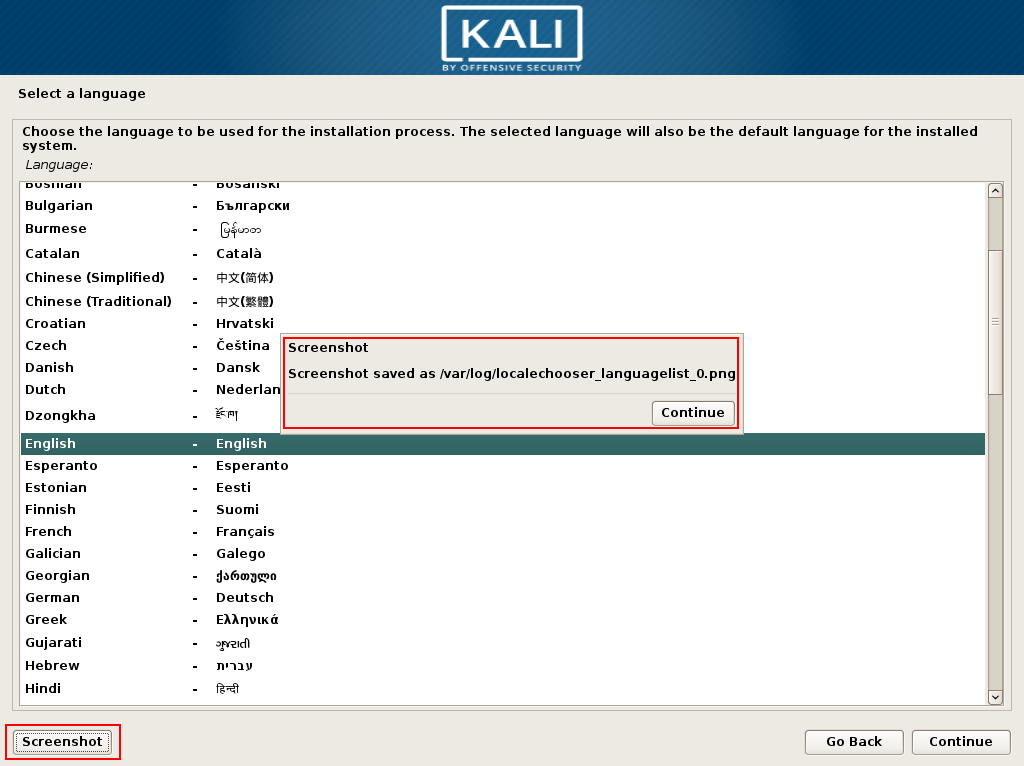
Note that several errors regarding not being able to find anything on SDA will scroll by; don’t worry about them. That’s normal for an empty disk. - Choose the installation language. I also want to draw attention to the Screenshot button; This appears on every page, so you can store install images for later retrieval:
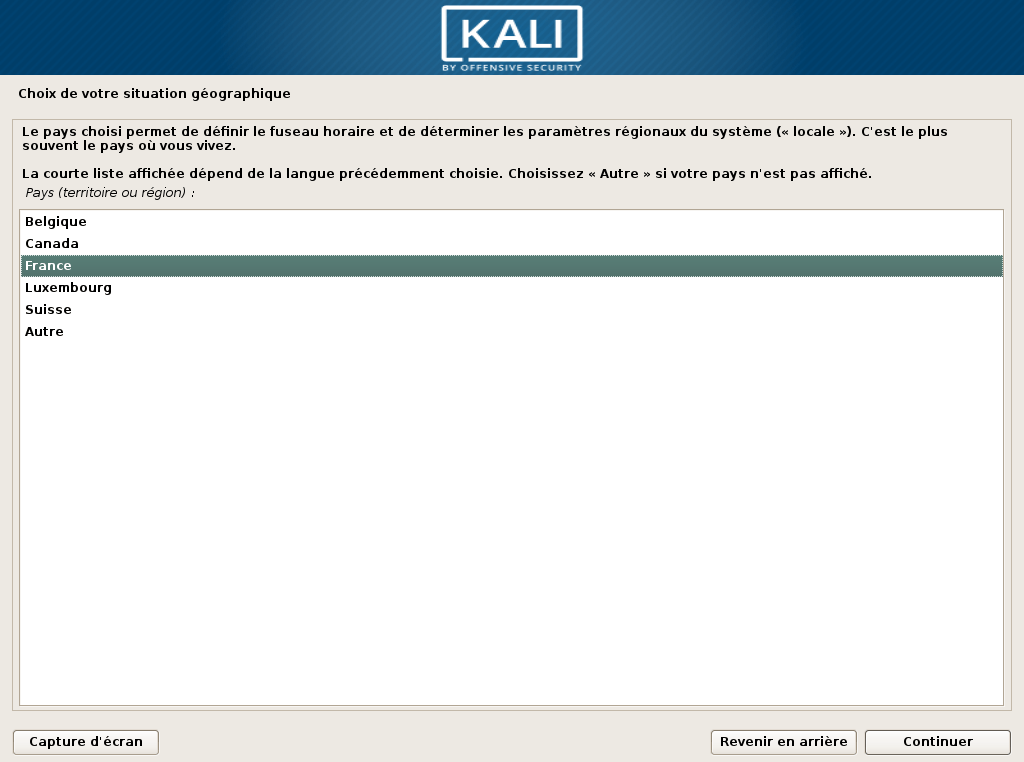
- Choose your location. Be aware that the options you see are determined by your language selection! The following two screenshots show the outcome of choosing English and French in step
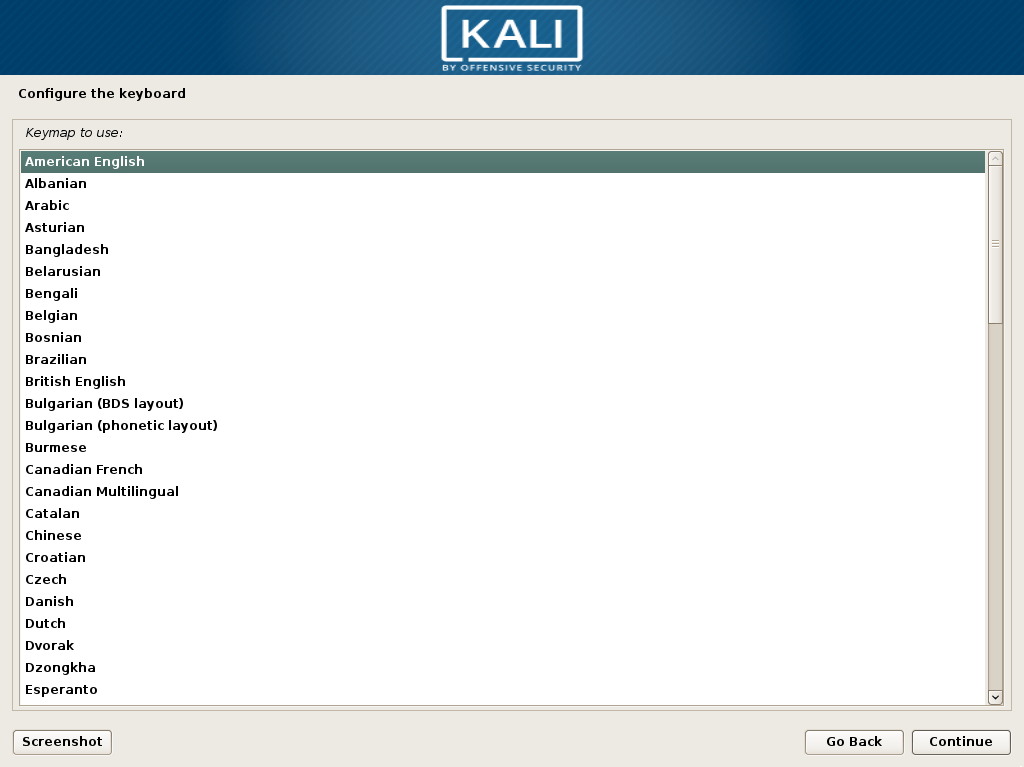
4. Choose your keyboard layout:
5. The installer will then load some files and perform basic network configuration. I noticed that it performed IP assignment from DHCP; I did not test to see what happens if it can’t reach a DHCP server.
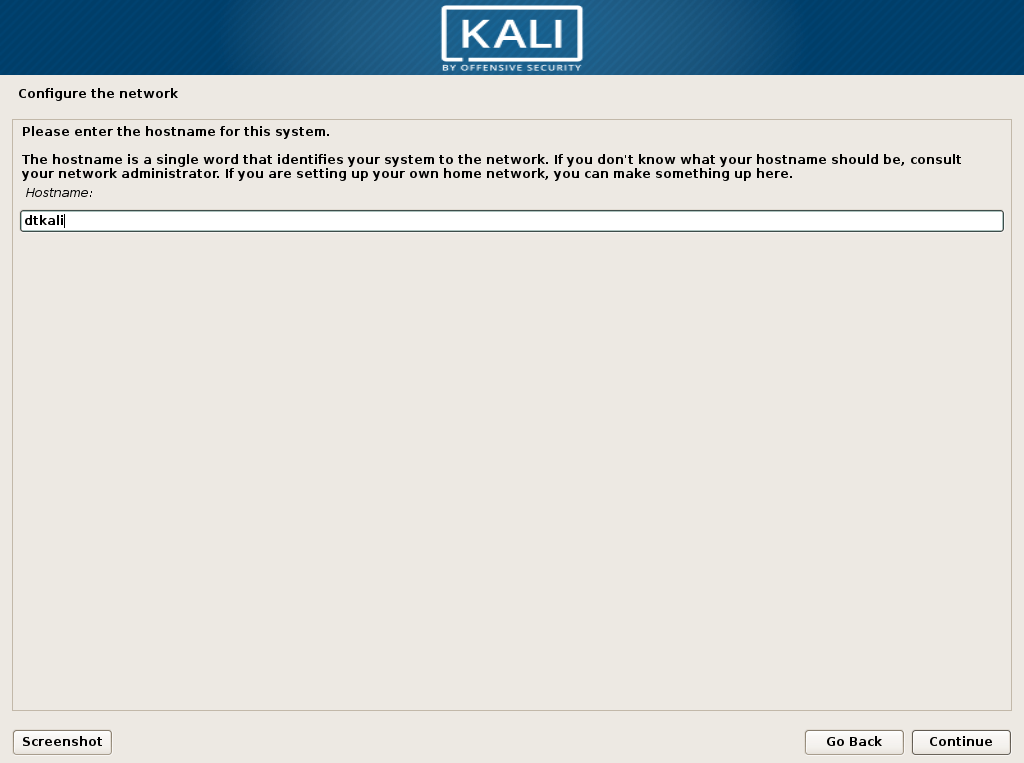
6. After the component load, provide a host name. It appears to automatically choose whatever name DHCP held for that IP last. Only provide the name, no domain.
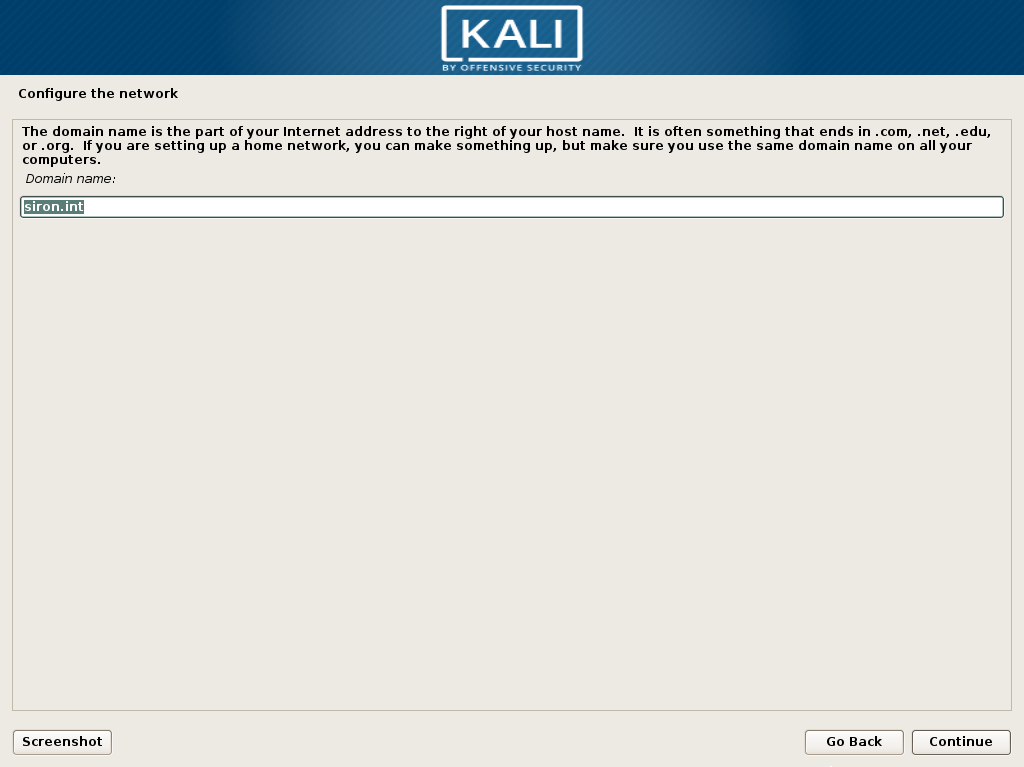
7. Provide your domain name. You can invent one if you aren’t using a domain, but you must enter something.
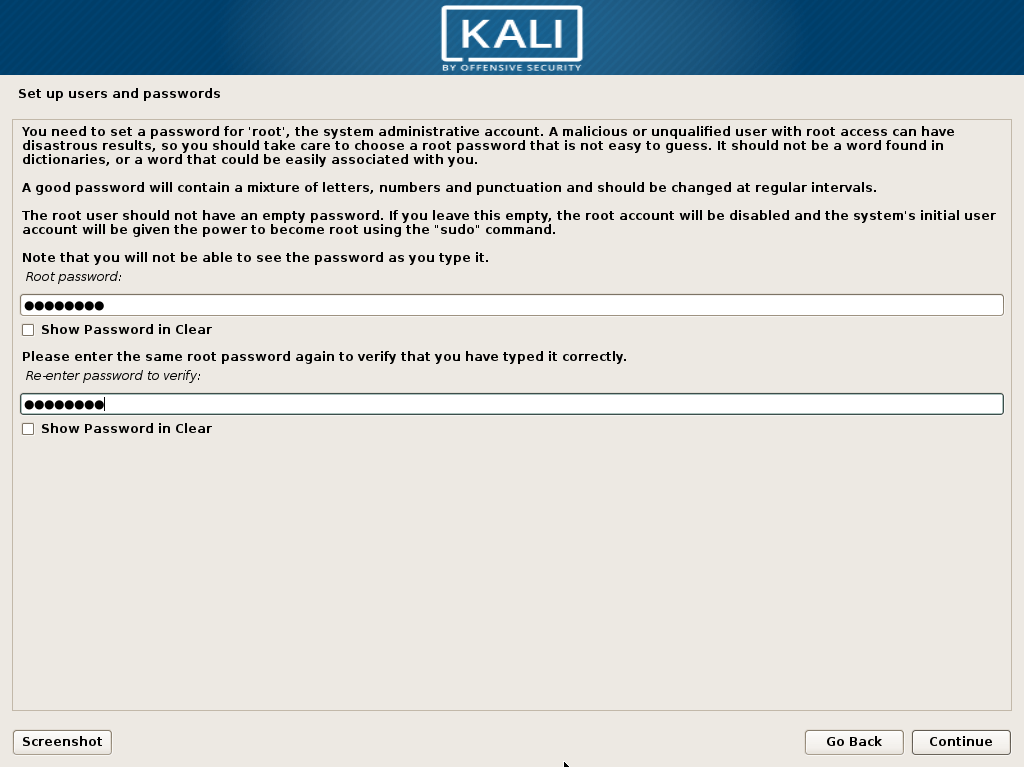
8. Enter a password for root. Even though it mentions user creation, you aren’t creating a standard user account like you would in other distributions.
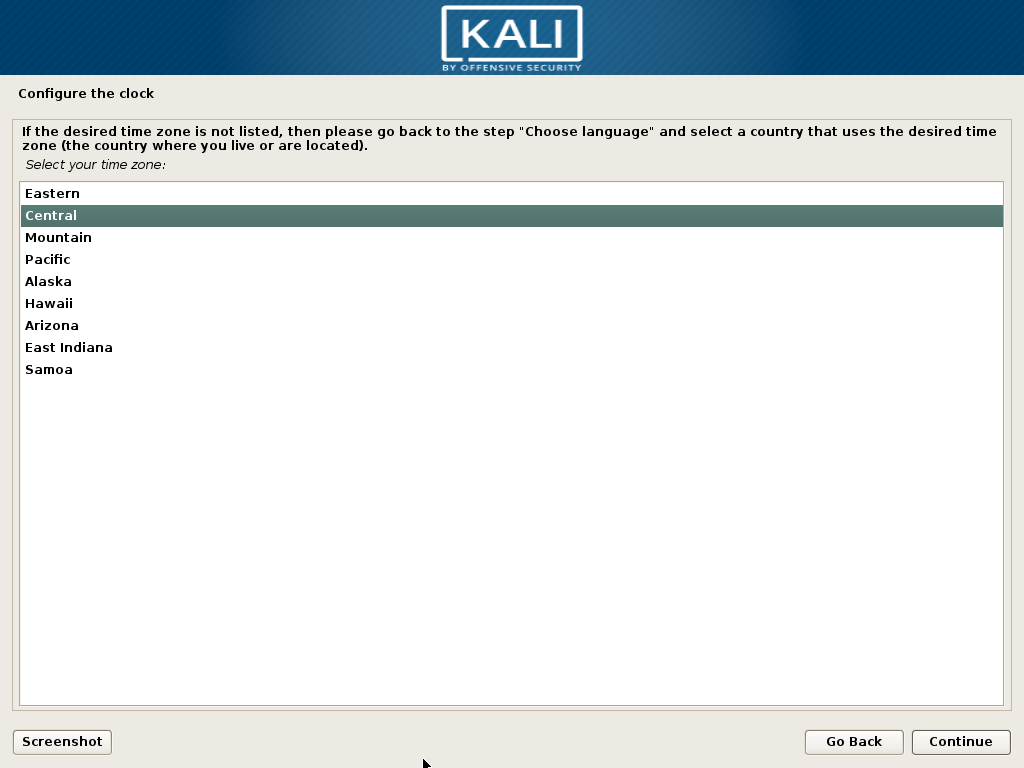
9. Choose your time zone. Options will be selected based on your earlier region choices. Why it appears at this point of the installer, I certainly do not know.
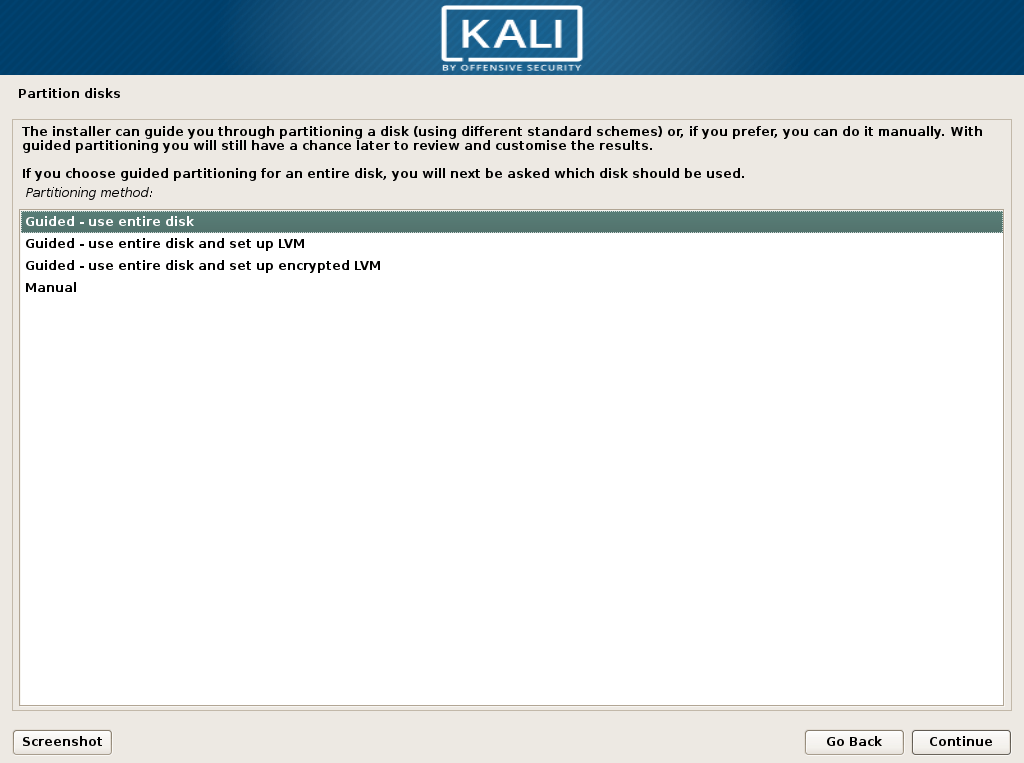
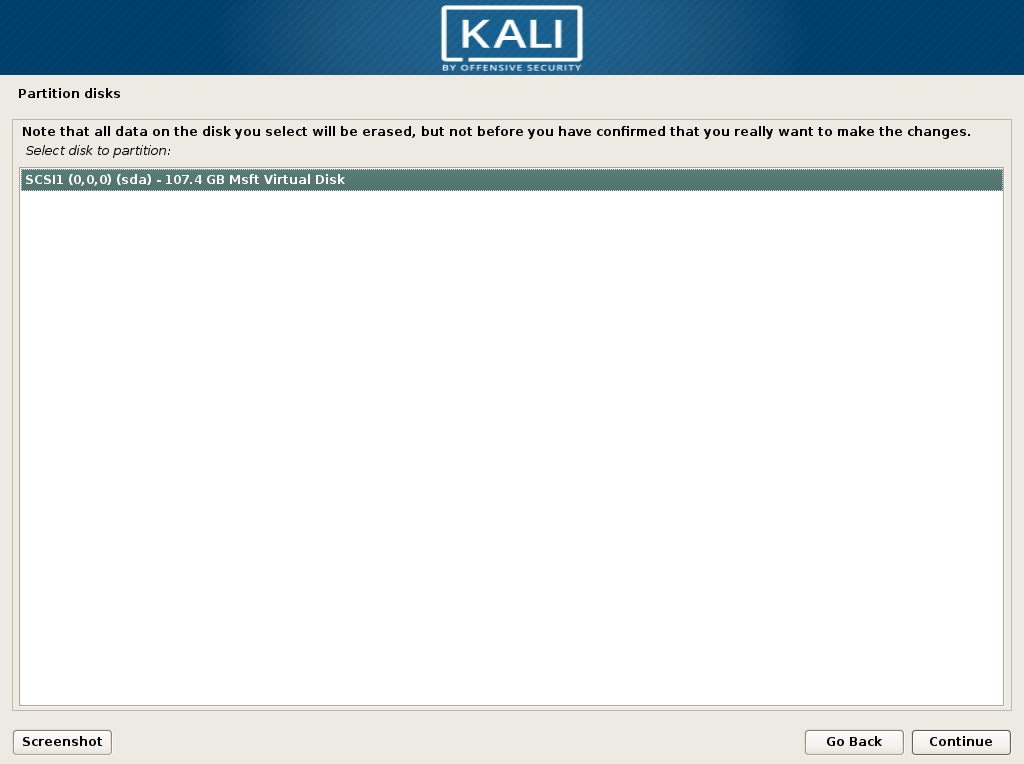
10. Choose how you want your disk to be laid out and formatted. I personally choose Guided – use entire disk because I’m not the biggest fan of LVM. Any of the first three choices are fine if you’re new and/or not especially picky.
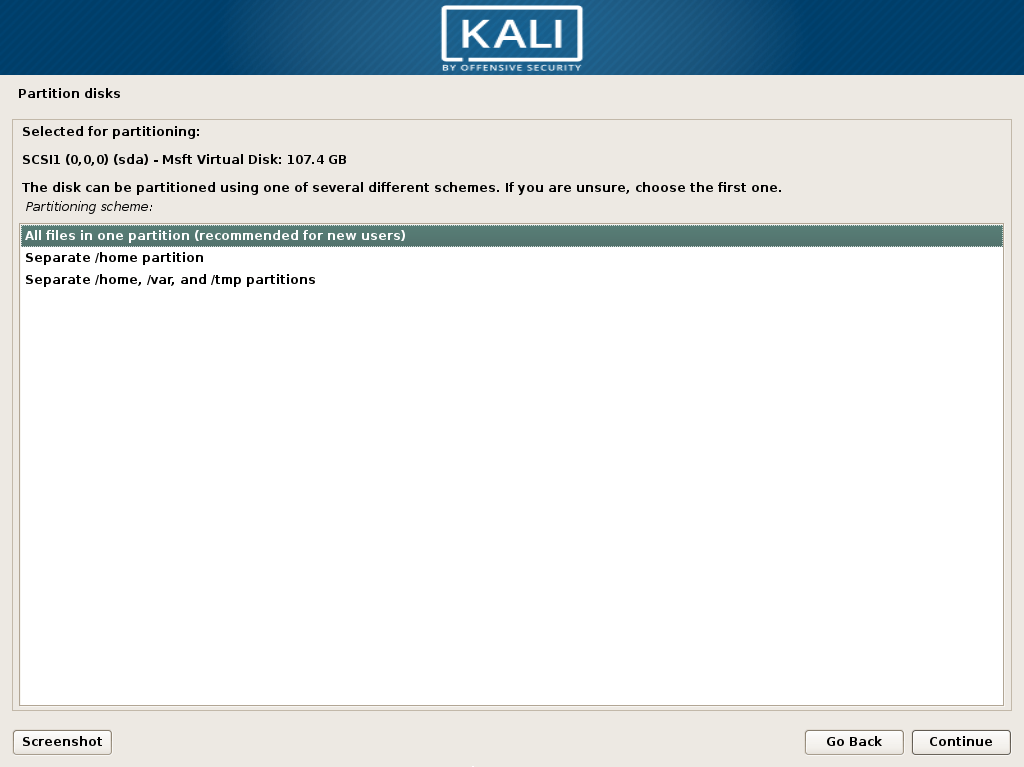
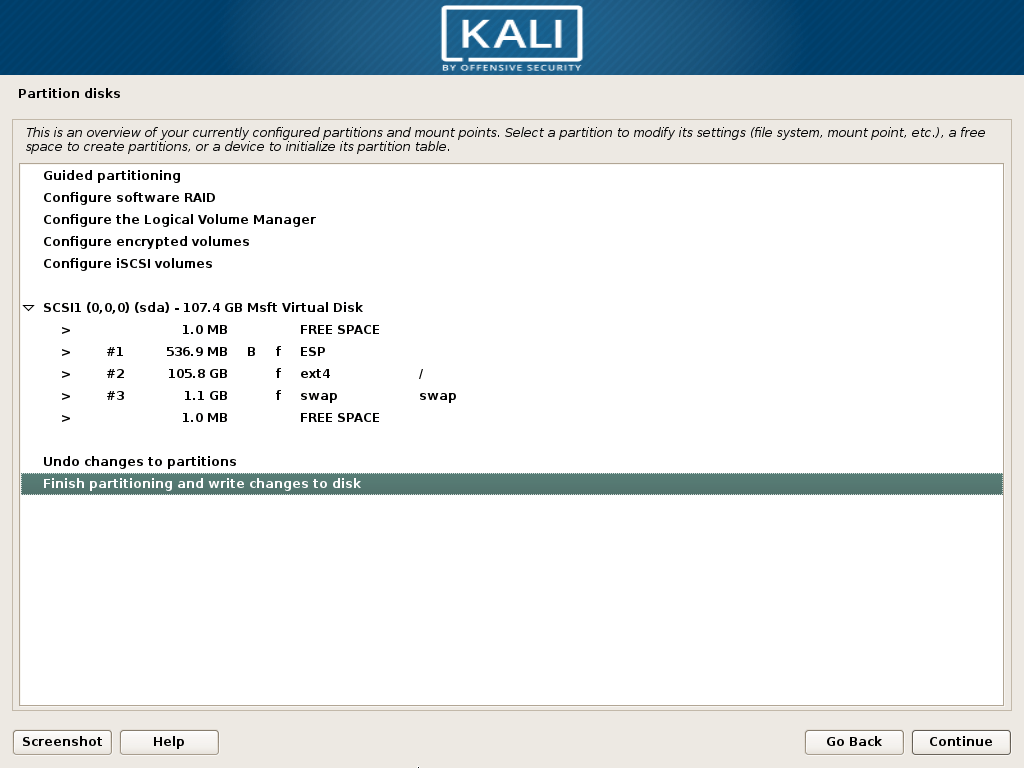
12. Then confirm partition usage:
14. And again… (this installer needs a lot of polishing):

15. Now, your formatting options will be applied and files will be copied. This will take a while and there will be more questions, so don’t go too far.
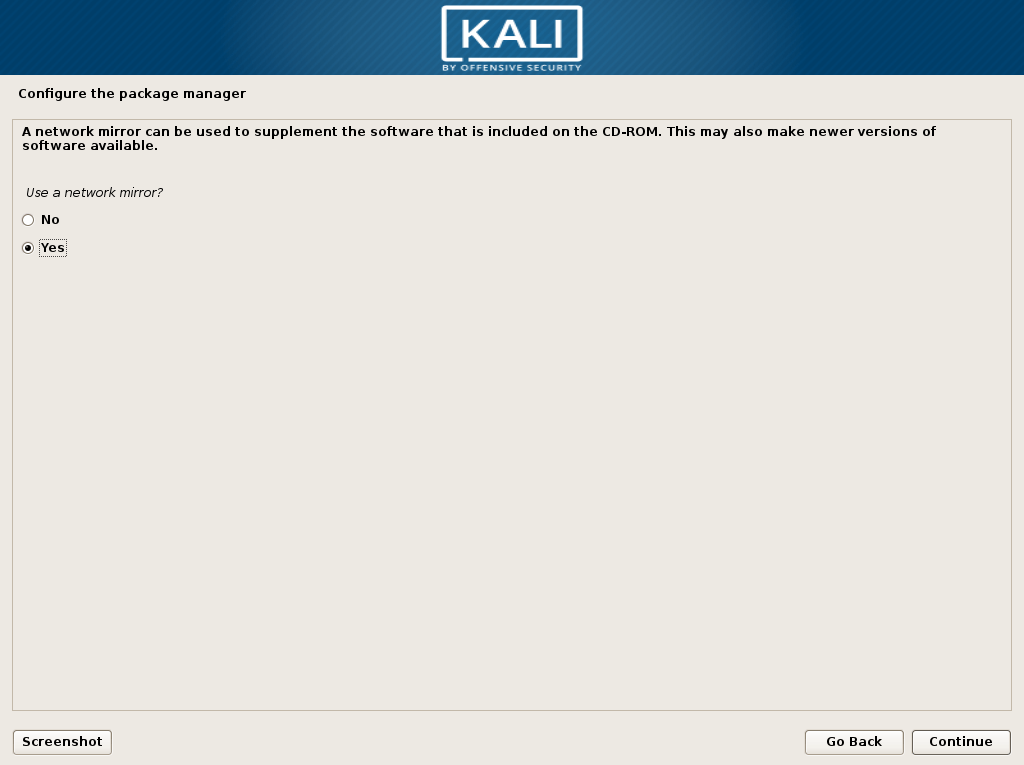
16. Now you need to choose whether or not you’ll allow software to be downloaded from the Internet (or a specially configured mirror). If you choose no, you’ll need to manually supply packages or add a repository later.
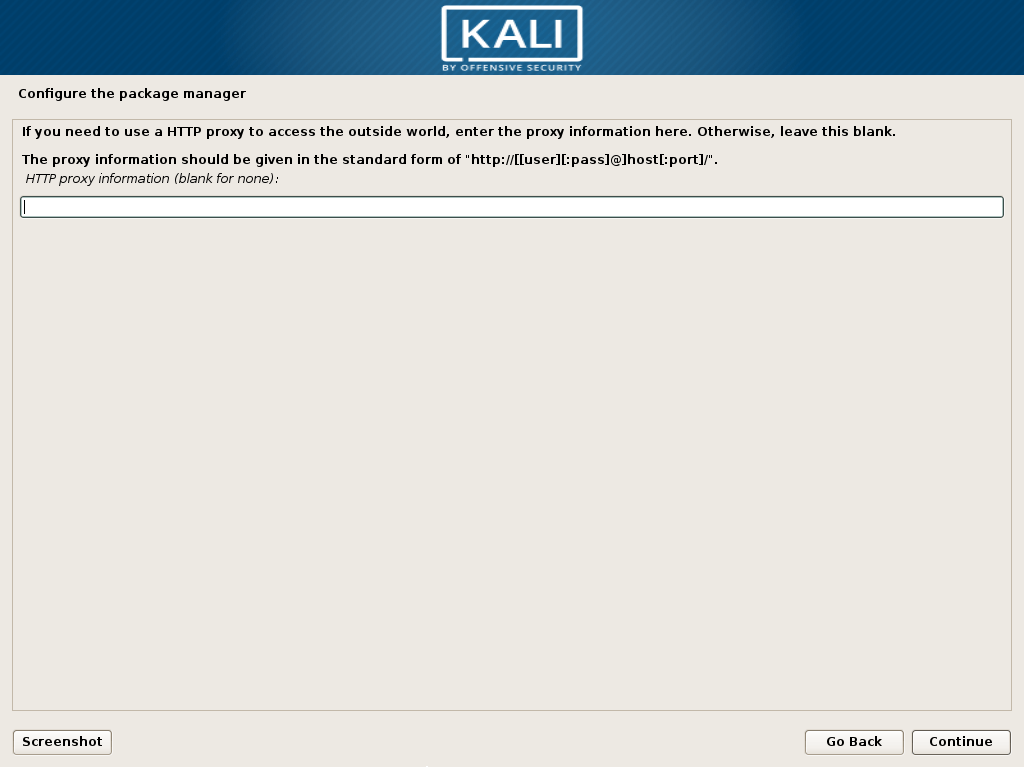
17. If you need to enter proxy information, do so now:
18. You’ll have a few more minutes of configuration, then what appears to be a completion screen.
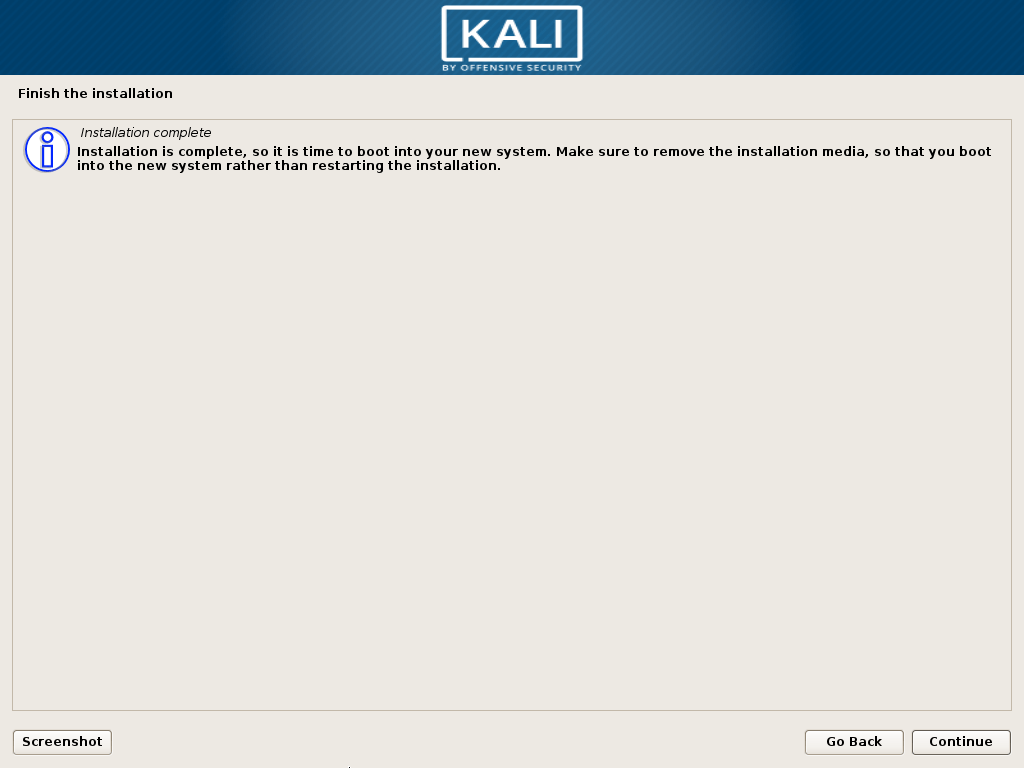
19. There’s still more stuff to do, though:
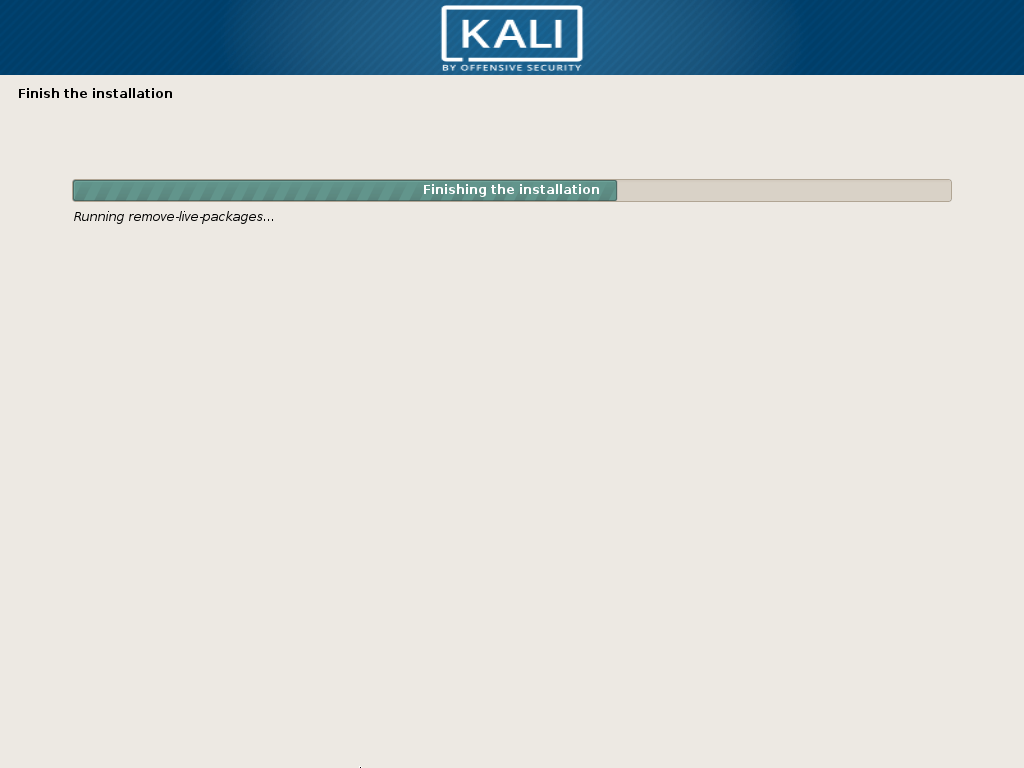
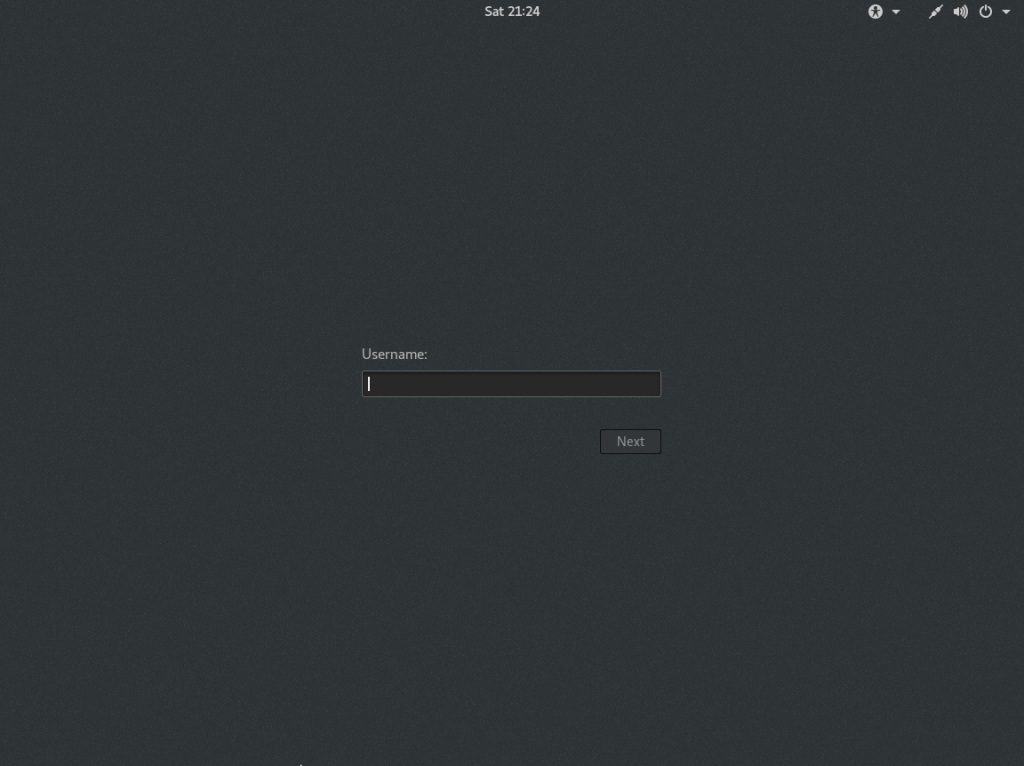
20. As soon as that part completes, the system will reboot and launch into your new Kali environment.
Getting Started with Kali
Here’s your login screen! Remember to use root, because you didn’t create a regular user:
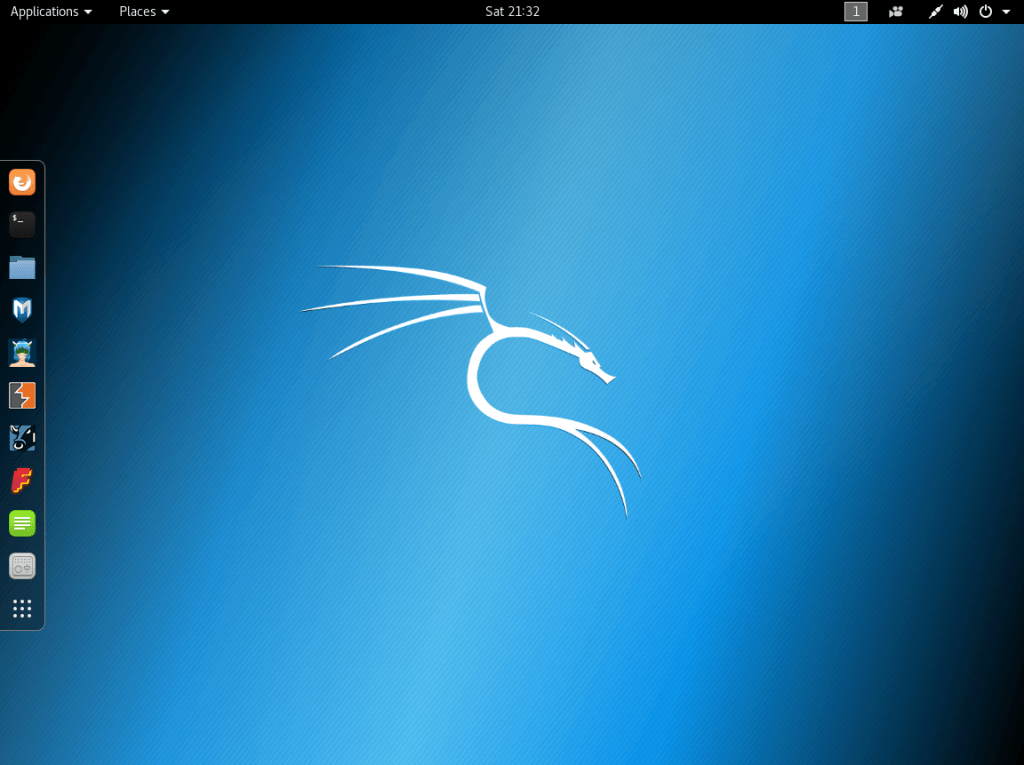
And finally, your new desktop:
Post-Install Wrap-Up
I know that you’re anxious to start exploring this wonderful new environment, but we’ve got a bit of housekeeping to take care of first with the Kali Linux Hyper-V installation.
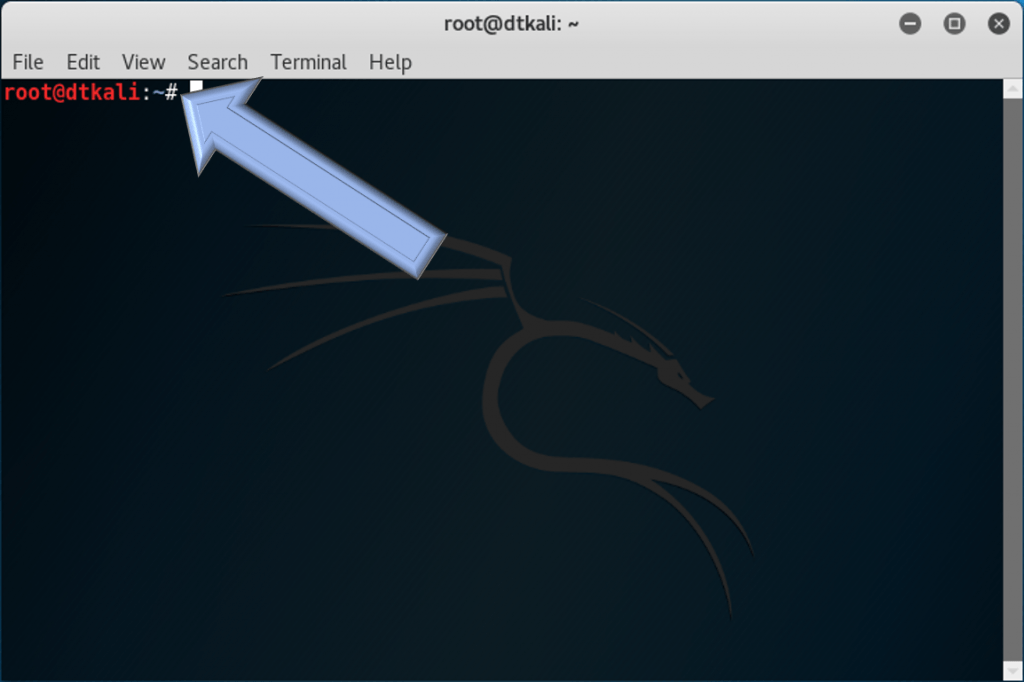
At the left, in the quick launch bar, hover over the second icon from the top. It should be a black square and the tool tip should say Terminal. Click it to launch a terminal window:
Since we’re running as root in the Kali Linux Hyper-V environment, the terminal will already be running with the highest privileges. You can tell by the # prompt as opposed to a > prompt.
Install Extra Hyper-V Services
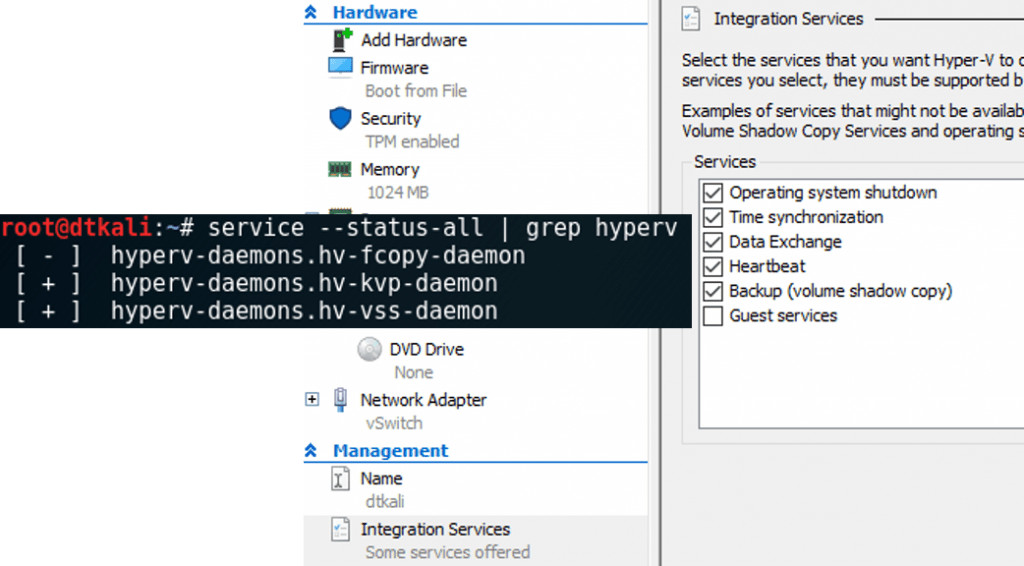
The required Kali Linux Hyper-V components are already enabled. Let’s add the KVP, VSS, and file copy services. Enter:
apt install -y hyperv-daemons
This installs the file copy, KVP, and VSS services for Kali Linux Hyper-V. As we will note below, the Hyper-V daemons are installed in later releases of Kali Linux. Whether or not they start depends on whether or not the relevant services are enabled. The default Hyper-V setting enables all except Guest Services, so all except the file copy daemon should start automatically. Use service –status-all | grep hyperv to find out:
Change the Scheduler to NOOP
Linux has an I/O scheduler, but Hyper-V has an I/O scheduler. Turn off Linux’s for the best experience.
Edit the GRUB loader:
nano /etc/default/grub
This will load the GRUB configuration file. Find the line that says:
GRUB_CMDLINE_LINUX_DEFAULT="quiet"
Change it to:
GRUB_CMDLINE_LINUX_DEFAULT="quiet elevator=noop"
Press [CTRL]+[X]. You’ll then need to press [Y] to save the changes, then [Enter] to indicate that you want to save the data back to the file you found it in. That will leave you back at the prompt.
And finally:
update-grub2 reboot
Exploring Kali Linux
You have now completed all of your installation and preparation work! It’s time to take Kali Linux Hyper-V for a spin!
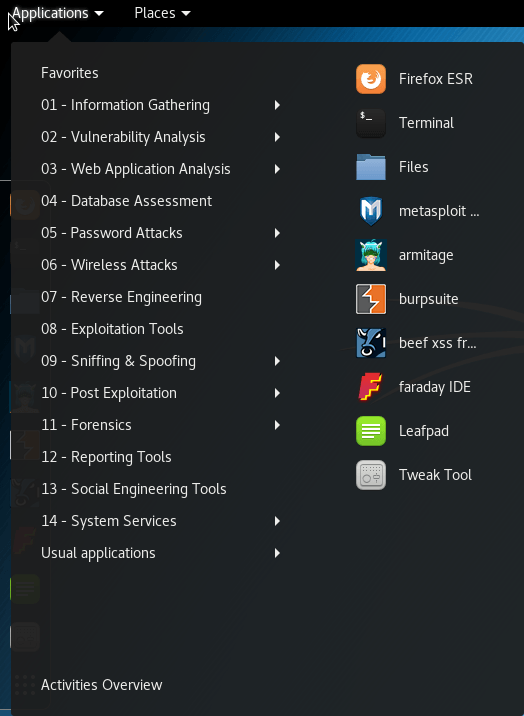
If I didn’t make this clear enough earlier, I’ll be crystal clear right now: I don’t know that much about penetration testing. I recognize many of the names of the tools in Kali, but the only one I have a meaningful level of experience with is Wireshark. So, don’t ask me what this stuff does. That’s why we have the Internet and search engines.
Let’s start with the boring things to get them out of the way. In the top right you’ll find some system status icons. Click and you’ll get the system menu:
- Hyper-V doesn’t (yet?) enable audio out of Linux systems, so the volume slider does nothing in Kali Linux Hyper-V.
- Where my screenshot shows Wired Connected, you’ll find your network settings. Click it to expand the menu where you can access them.
- Where my screenshot shows Proxy None, you can click to access your proxy settings.
- Where my screenshot shows root, you can click for a Log Out option and a link to your logged on user’s account settings.
- The wrench/screwdriver icon takes you to the system settings screen. It’s analogous to Windows’ Control Panel. I don’t think you’ll need me to explain those items, so I’ll just recommend that you create users aside from root if you intend to use this desktop for more than just pentesting.
- The padlock icon locks the desktop. From a lock screen, just press [Enter] to get a login prompt.
- The power button icon takes you to a cancel/restart/shutdown dialog.
The Usual Applications group gave me a chuckle. You’ll find all the things that you’d find on a “normal” distribution there.
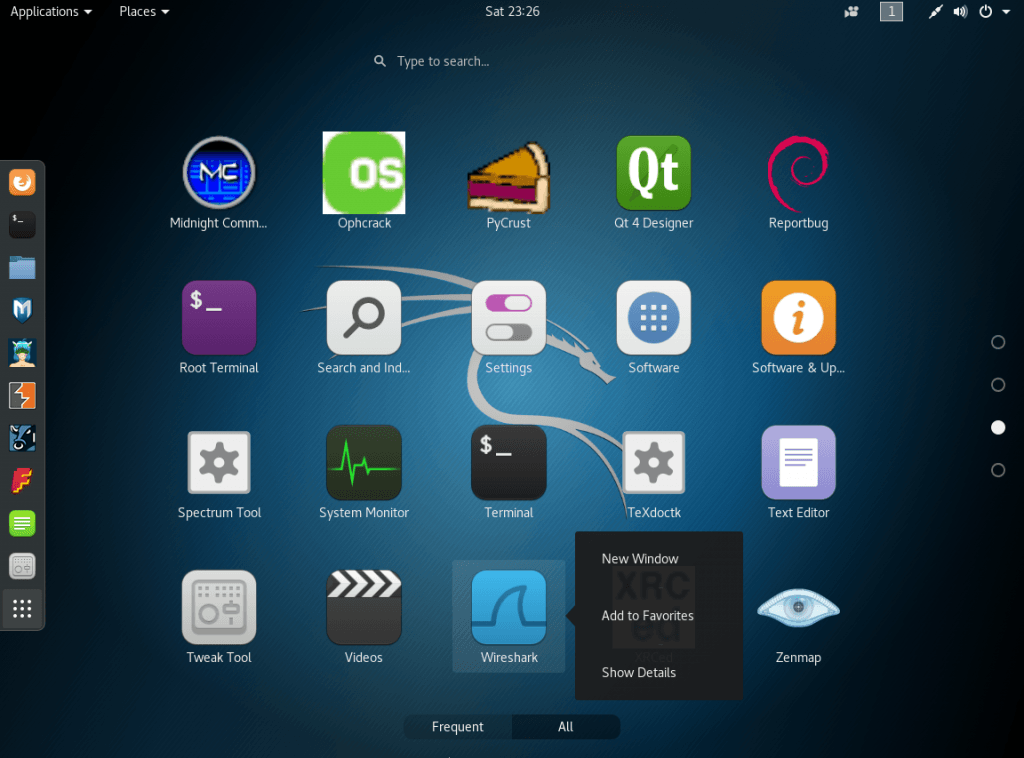
You met the quick launch dash earlier, when you started the terminal. It sits at the left of the screen and contains everything marked as a favorite. It will also include icons for running applications. The nine-dot grid at the bottom opens up Kali/Gnome’s equivalent to Windows’ Start menu. From there, you can launch any item on your system. You can also add items to the Favorites/Dash area:
Kali Linux Hyper-V Enhanced Session
A Hyper-V Enhanced Session provides more robust features and capabilities when interacting with a guest virtual machine. As a note, Kali Linux Live Image 2021.3 and higher come with the Hyper-V daemons preinstalled. So keep this in mind with your Kali Linux Hyper-V installations that the daemons installation walkthrough shown is already installed with the latest releases of Kali.
As part of the process of how to install Kali Linux on Hyper-V, there are still enhancements you can make for interacting with Kali Linux, including changing the transport type. See the official Kali Linux walkthrough here: Installing Hyper-V Enhanced Session Mode (Guest Tools) | Kali Linux Documentation.
Get Testing!
You’ve got your shiny new Kali install ready to roll. Kick the tires and see what you can accomplish.
Oh, and remember that we’re the good guys. Use these tools responsibly.
Final Notes
Overall, the process to install Kali Linux in Hyper-V is fairly straightforward. Using the script shown in the post, you can quickly create a new Hyper-V virtual machine for the Kali Linux installation. After downloading the ISO image, the installation process is similar to any other operating system install. Hyper-V is a great platform to run robust security tools like Kali Linux Hyper-V installations.


Not a DOJO Member yet?
Join thousands of other IT pros and receive a weekly roundup email with the latest content & updates!











24 thoughts on "How to run Kali Linux on Client Hyper-V"
Hello,
I have followed you tutorial, but I am running a VM on windows server 2012 r2. When installation starts I get an error saying: kernel panic – not syncing: machine halted.
Any feedback would be appreciated.
Otherwise great tutorial, thank you for sharing it.
That’s really weird. I don’t see any useful search results for that particular error. The important part is “machine halted”. Make sure that the VM is configured correctly (has writable storage attached) and isn’t using secure boot. Other than that, I’m not sure. If I get some time, I will try to replicate the problem.
Thank you for the secure boot tip, I could not figure out why it wouldn’t boot.